
It’s great how the site has a Security Scenarios section too, where it offers personalized security tips for specific audiences (activists, academic researchers, journalists, and more). This is a free service that lets you upload images to share them with other people. It’s great for people who live in or travel through restrictive countries to securely access and use image hosting and sharing services, which might be unavailable.
How To Access The Dark Web Using Tor

Yes, the Hidden Wiki remains one of the most accessed community-curated directories for .onion links, though users must verify each link’s authenticity. By carefully following these instructions and maintaining responsible browsing practices, safely exploring the dark web can be straightforward and secure. With these precautions in place, you’re ready to start your journey into the world of .onion sites. To access .onion websites securely, you’ll need the Tor Browser, a privacy-focused tool designed specifically for anonymous browsing. Here’s a straightforward guide to help beginners get started safely and efficiently.
FAQs About The Dark Web And Onion Sites
This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. Using the Tor browser is simple, but knowing when to fire it up is more complicated. Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual.
For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN.
What Are Dark Web Websites?
However, be aware that mobile devices can also be vulnerable to viruses and malware. Cyble plays a key role in this landscape, offering AI-powered threat intelligence and digital risk protection. As we enter 2025, these tools are adapting with improved security and functionality to meet user needs. Dark web forums are online communities where individuals participate in discussions on a wide range of subjects, from technology and privacy to more illicit matters.
Why Use The Hidden Wiki Instead Of Google?
It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. Whited’s rule of thumb is to use the Tor Browser instead of Private Browsing Mode or Incognito Mode. “Contrary to what most people think, these modes do not actually protect your privacy,” she says. Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser. The spy agency is hoping to securely and anonymously collect tips, though its entire website, including job listings, are available on the onion service.
A VPN encrypts your internet traffic before it enters the Tor network, hiding your Tor usage from your internet service provider and shielding your IP address from the first Tor relay. This setup can help prevent network-level surveillance and reduce risks in environments where Tor use might be flagged or restricted. Choose a trustworthy VPN service that has a strict no-logs policy and supports connection without DNS leaks.
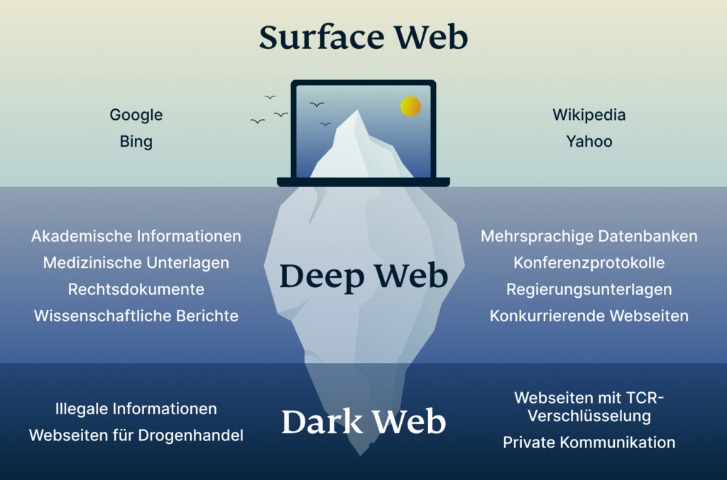
Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. An easy way to find content on the dark web is to receive a link from someone who already knows about it. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Look no further if you want good music while navigating the dark web.
What To Do If You See Something Illegal
It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. However, this feature is only available on iOS, Android, and Windows. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities.
DuckDuckGo — A Dark Web Search Engine
When you use it, all the web traffic automatically routes through Tor. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace.
- Avoid clicking on suspicious links, disable JavaScript where possible, and never share personal or financial information on dark web sites.
- This space for private free speech also carries the risk of exposing you to harmful content.
- Drug dealers can sell to customers across the world, not just locally.
- We aim to be the go – to destination for industry – leading news, in – depth analysis, and practical advice.
- Rather, it returns a list of posts looking for advice on how to hack Facebook accounts, where to buy stolen Facebook accounts, and so on.
The platform’s vast repository of tools, combined with its dedication to open-source development, makes it an essential stop for those navigating the Tor network. Offering a plethora of resources, from software packages to documentation, the Debian Project’s .onion platform is a treasure trove for tech enthusiasts and developers. However, its .onion service underscores the agency’s recognition of the importance of secure, anonymous browsing. When accessed via the Tor network, Tails provides an array of tools optimized for security, from web browsers to email clients. Whether users are seeking specific information, resources, or merely exploring out of curiosity, Ahmia delivers comprehensive and relevant search results. Prioritizing user privacy, it offers coin mixing services to ensure the anonymity of Bitcoin transactions.
A What Are Onion Websites?
It is a Swiss-based company (privacy-friendly country), and all its tools are open-source, meaning anyone can test its vulnerabilities. ProPublica is a prominent investigative journalism platform on the regular and dark web. This duality allows users to choose whether to access the platform openly or anonymously.
- We’re back with another video in our Webz Insider video series on everything web data.
- Husain is also a part of the vpnMentor Cybersecurity News bulletin and loves covering the latest events in cyberspace and data privacy.
- It’s impossible to access the dark web with a regular browser like Chrome or Safari.
- Your safety on the dark web depends more on cautious browsing habits than any single security tool.
- Therefore, you will always find updated search results while using this service.
- To access Tor from your computer, download the Tor Browser at TorProject.org/download/.
The Dark Web isn’t a place for everyone but it’s worth exploring some parts of it. For those who may be a little faint of heart – we have listed 50 Legit Dark Web sites you can visit. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts.
Offering a well-organized list of links spanning various categories, TorLinks serves as a reliable guide. Students, researchers, and academics flock to Sci-Hub on Tor to access invaluable resources without the burden of hefty fees. Here are some things to keep in mind while browsing your favorite dark web websites. The anonymous group behind Tunnels alleged that the materials were produced while exploring the forbidden tunnels, built underneath some of the most prestigious American Universities. No info is available on the explored institutions or how these sections can be accessed.



