Built-in advanced protection features, like parental controls and ad blocking, offer even more control. Data inside the tunnel is encrypted, ensuring that only the intended recipient (the VPN server) can decrypt and understand the information. Authentication ensures a secure connection between the VPN client (i.e., your router) and the VPN server. Mathematical processes verify the identities of both ends, ensuring that they communicate exclusively with each other.
Understanding The Impact Of Xfinity WiFi On The Darknet Market
It allows Comcast customers to access the internet on the go through a network of millions of hotspots across the country. Customers logging onto their Xfinity accounts have been required to change their passwords to protect their accounts. They also are urged to set up two-factor, or multi-factor, authentication and to change passwords for other accounts that share the same username and password or security question.
If your device fails to meet these requirements, you might face issues like software crashes or decreased system performance. Yes, the free antivirus service provided by Xfinity, also known as Norton Security Online, can be used across different operating systems including Windows and macOS. You may need to enter your Xfinity username and password during the installation process. Welcome to our latest tech insight – today, we delve into the world of cybersecurity with a focus on Xfinity. If you can’t use smartphone tethering and absolutely must connect to public Wi-Fi, we recommend that you at least use a VPN (Virtual Private Network).

Discover The Hidden Web: A Guide To onion Links
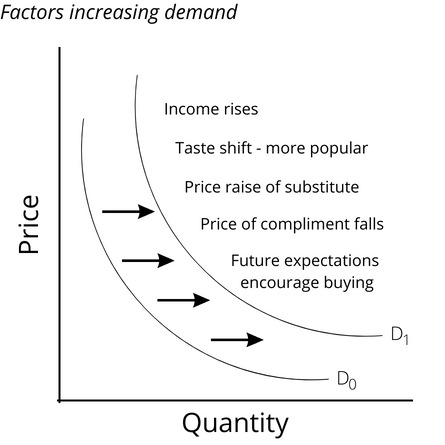
Xfinity WiFi is a service provided by Comcast that allows Xfinity internet customers to access WiFi hotspots throughout the United States. These hotspots are available in public places such as parks, cafes, and shopping centers, as well as in private homes of Xfinity customers who have opted to participate in the program. Comcast’s High-Speed Internet network is a shared network, which means that our customers share upstream and downstream bandwidth with their neighbors. Thus, when a relatively small number of customers in a neighborhood place disproportionate demands on network bandwidth, they can heavily contribute to congestion that degrades their neighbors’ Internet experience. Although Comcast does its best to prevent IP address spoofing, there are situations where applying uRPF checking is not feasible or practical.
Risks Of Using Xfinity WiFi For Darknet Activities

Finally, downloading a Usenet file doesn’t mean you have to seed it for other internet users afterward. Legally, this makes you less of a target because you’re not supplying strangers with copyrighted content, but at the same time, you’re consuming fewer computer resources and internet bandwidth. We did this research to help the public understand just how much their personal data is worth.
Your Internet Service Performance
She previously covered the public cloud at CRN after 15 years as a business reporter for the Boston Herald. Based in Massachusetts, she also has worked as a Boston Globe freelancer, business reporter at the Boston Business Journal and real estate reporter at Banker & Tradesman after toiling at weekly newspapers. We see the benefits of open finance first hand at Plaid, as we support thousands of companies, from the biggest fintechs, to startups, to large and small banks. All are building products that depend on one thing – consumers’ ability to securely share their data to use different services.
Does Xfinity WiFi Affect Darknet Market Transactions?
This includes utilizing encryption tools, practicing good opsec (operational security), and avoiding any actions that could potentially expose their real identities. Tor has the advantage of being an open-source network and is the most user-friendly option available which explains its wide use. Onion routing covers messages in layers of encryptions which are peeled away as it travels from node to node.
Stanford Health Network Announces MOVEit Breach
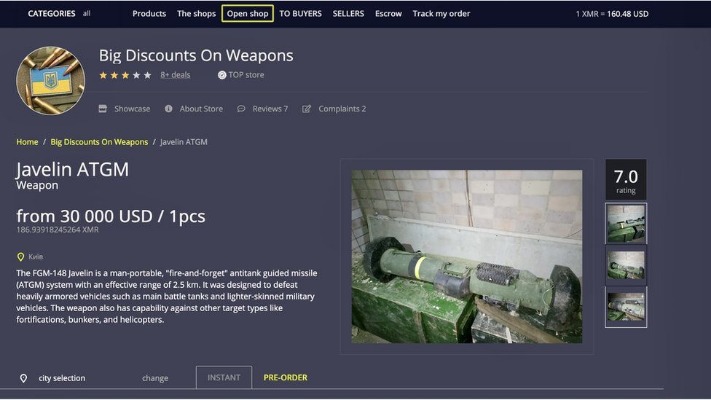
Fintech offers innovative products and services where outdated practices and processes offer limited options. We advocate for modernized financial policies and regulations that allow fintech innovation to drive competition in the economy and expand consumer choice. With XClass, Comcast is clearly trying to prepare for a future post cable TV, with cord cutters ditching cable boxes for smart TVs to access streaming services. The term “darknet market” refers to a part of the internet that is not indexed by traditional search engines. It serves as a platform for the trade of various goods and services, often illicit in nature. These sites could have malware, spyware, ransomware or viruses that could infect devices and make them at risk to personal data collection, blackmail or attacks on other computers and networks.
Darknet markets — also known as cryptomarkets — provide a largely anonymous platform for trading in a range of illicit goods and services. Incognito or private mode will keep your local browsing private, but it won’t stop your ISP, school, or employer from seeing where you’ve been online. In fact, your ISP has access to all your browsing activity pretty much no matter what you do. Xfinity is a popular broadband service in the United States, providing high-speed internet, cable television, and telephone services. It uses a combination of fiber and coaxial cables to deliver its internet services, making it one of the most widely used ISPs in the country.

Q: Are There Any Alternatives To Using Xfinity WiFi For Accessing The Darknet Market?
This means that if law enforcement agencies were to investigate illegal activities on the darknet market, they could potentially track down the user through their Xfinity WiFi connection. To mitigate such issues, darknet market users should ensure they have a stable and reliable internet connection with adequate bandwidth. Considering alternative internet service providers or using dedicated private networks might be viable options to maintain optimal performance. Yet each time, another string of darknet markets pop up to hoover up the users and continue working. Even when connecting to sites that encrypt their traffic or using VPNs, ISPs can still collect the domains their customers connect to and analyze their browsing behavior.
Can You See Deleted Search History On WiFi Bill?
- However, for advanced, real-time protection and better customer service, you might want to consider a paid antivirus service.
- The anonymity offered by the darknet makes it difficult for law enforcement agencies to track down its users.
- Though it depends on the device, routers keep limited logs and write over old logs when they run out of memory capacity.
- Xfinity WiFi is a broadband internet service provided by Comcast, known for its extensive coverage and high-speed connectivity.
Stolen documents of this nature – intercepted in the mail, for example, or stolen and sold to criminals by corrupt officials – fetch very high prices. UK passports, marriage and birth certificates all trade for around £2,000, but can fetch as much as £5,000. The higher value is because it’s easier to realize the value of debit cards into cash, and because accounts with high balances are being put up for sale more often. Notable price surges include Airbnb (£20), Facebook (£14) and PayPal (£84.50) due to the sheer scope of potential fraud that can be committed by scammers in possession of these accounts. If you fall delinquent on an account and the creditor sends it to a collection department or agency that reports to the credit bureaus, however, that will hurt your scores.
Social networking services such as Facebook have created new ways to socialize and interact. Users of these sites are able to add a wide variety of information to pages, pursue common interests, and connect with others. Yes, Xfinity does maintain logs of user activities, which can include browsing history. Engaging in darknet market activities can raise red flags, potentially leading to further scrutiny. You’ll be able to do so without the performance problems of inferior VPNs (particularly free VPNs) such as lag and buffering. Data caps limit how much total data you upload and download after you reach a certain threshold.