Yura devoted a lot of energy to defending the website’s credibility. A California-based person going by name Thcjohn2 had written to the website offering his services as an assassin. “I am broke (of course), and am looking for quick cash,” Thcjohn2 wrote. “I have military training (US Navy).” Instead of taking him up on his offer, Yura had asked Thcjohn2 to make videos of burning cars to intimidate Monteiro and other critics. He then asked him to enact and video a fake murder, with the help of a friend and a replica gun. In the following months, several videos of balaclava-clad thugs firing guns and talking up Yura’s assassination websites would pop up online.
The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from. Then, simply click the operating system that you are using and download the file. The site offers downloads for macOS, Windows, Linux, and Android. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you.
Are Onion Sites Safe?
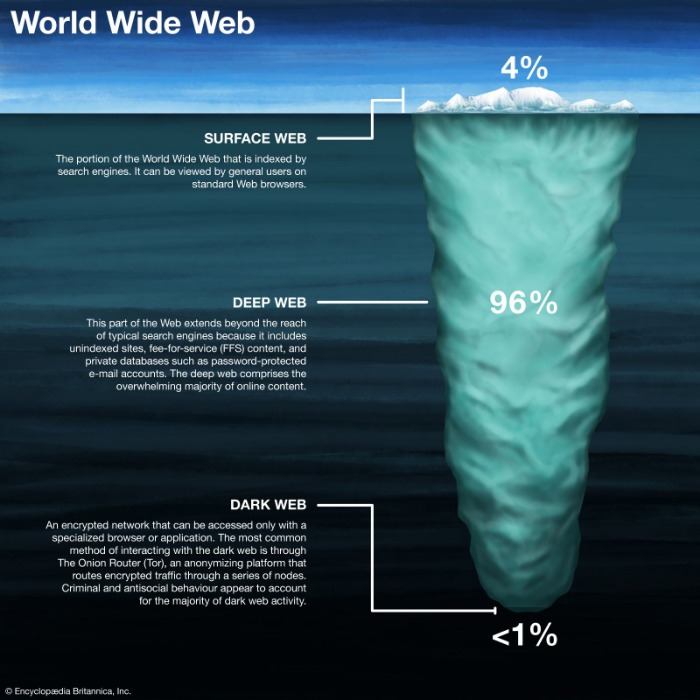
But before we get into that, it’s important to understand the differences between the surface web, deep web, and dark web. So, even though it does exist on the internet, Google doesn’t index any of these pages or content. Let’s summarize the most important points from this guide on how to access the dark web. It also has 10 simultaneous connections, support for all devices, and server obfuscation that works in China. You’ll appreciate its added features, such as Threat Protection, which shields you from malware and trackers.

These professional killers utilize various strategies to carry out their illegal activities discreetly. One way they ensure anonymity is by using encryption tools and anonymous browsing software to conceal their IP addresses. By doing so, they make it extremely difficult for law enforcement agencies to trace their online activities back to their physical location.
Tor Websites: 10 Links That Offer A Safer Browsing Experience
As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
The site has allegedly generated gobs of money, luring in thousands of clients with its offers to provide a variety of gruesome services—not just executions, but also beatings and torture. As a final conclusion, murder for hire services are, indeed, available on the dark web. Whether you’re interested to hear stories, conduct an interview or simply need such services, there are ways to get in touch with people. While there are, indeed, many cases of murder for hire over the dark web, the truth is this is a very sensitive topic. People wouldn’t do it randomly with strangers unless they’re desperate. You can find plenty of ads for hitmen, many of them authentic, some of them scams.
Searching For A Hitman In The Deep Web
Once you have the Tor Browser installed and optionally connected to a VPN, you can access the Hidden Wiki by entering its .onion URL directly into the browser’s address bar. Unlike regular websites, .onion addresses are long, complex strings of letters and numbers designed for anonymity and can be difficult to remember. Therefore, users often rely on trusted directories or updated links shared on community forums to ensure they access legitimate sites. Copy the .onion link carefully to avoid mistakes, as typos can lead to error pages or potentially malicious sites designed to impersonate the Hidden Wiki.
Illegal Pornography

To look at it in a different way, it makes up between 90% and 95% of the internet. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Site operators can also submit their own .onion sites for indexing. The Deep Web refers to web data you can’t find using a search engine like Google. Unlike the Dark Web, the hidden corner of the internet often used to conduct illicit or anonymous activity, anyone can get to the Deep Web safely using a regular browser.
Should I Only Use A VPN To Access The Dark Web?
- Staying safe on the dark web requires even more vigilance than the public internet.
- When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI.
- Website addresses that end in “.onion” aren’t like normal domain names, and you can’t access them with a normal web browser.
- EscrowBay offers escrow services tailored to dark web transactions, holding funds securely until both buyer and seller confirm satisfaction, reducing fraud.
- It’s particularly useful for journalists, whistleblowers, and those who urgently need to send or receive confidential data.
However, unlike commercial search engines, This is run by a confederation of volunteers. The search engine provides several special features beyond the original word. These include weather forecasts, maps, calculations and Boolean operations as inclusion or alternatives among others. Without his scamming, some lives would have been at risk and some people plotting murders would still be around.
OnionDir offers a privacy-first approach to dark web directories. It deliberately avoids any tracking or logging of user activity, providing a minimalistic interface that loads quickly over Tor. While it may not have as extensive a listing as some other directories, OnionDir focuses heavily on trusted, vetted links.
How To Get On The Dark Web Safely (Extensive Tutorial)
In 2020, I was slingshotted into a desperate race against time to save the lives of people I’d never met, from all over the world. For example, I looked up google.com and was able to find a snapshot of Google’s home page from 2008. Archive.today allows you to take a snapshot of a web page, which will remain online even if the original web page disappears. The site saves text and images, but it can’t save videos and sounds. This information can be used to target ads and monitor your internet usage. In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep.
Can You Access The Dark Web With A VPN?
Developed by the Freedom of the Press Foundation, the dark web site allows users to privately submit documents and sensitive materials without revealing their identity. ZeroBin is a minimalist paste-bin tool that allows users to share text securely and privately on the Tor network. Insights like these help researchers and advocates understand how and why Tor is being used. With this info, the wider online community can grasp Tor’s impact and its ability to provide secure and anonymous internet access. Although Hidden Answers offers an outlet for anonymous dialogs, users should stay cautious while browsing. Posts on controversial or even illegal topics are fair game, so the Tor website is a double-edged sword.
Most importantly, look for a reputable market and it should have an escrow service. Basically, your digital coins will be held by the market administrator until the service is delivered. When the mission is complete, the money will be released to the hitman. Additionally, using anonymous browsers like Tor can further enhance your privacy by routing your internet traffic through multiple servers, making it difficult for anyone to trace your online presence. Furthermore, hitmen may employ the use of intermediaries or mediators to facilitate their transactions.
Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. The US Supreme Court has indicated that even casual browsing could lead to legal consequences. Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations.