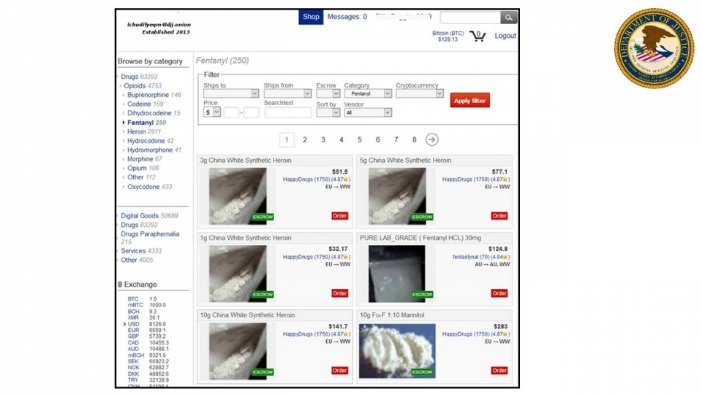
What I like is their no-fentanyl rule—shows they’re trying to keep things less messy. The site’s easy to use, with filters that actually work and a forum where folks swap tips. Word is, they’re pushing digital goods big-time next year—think stolen logins and cracked software.
‘It’s Happening Everywhere’: 1 In 3 ICE Detainees Held In Overcrowded Facilities, Data Show
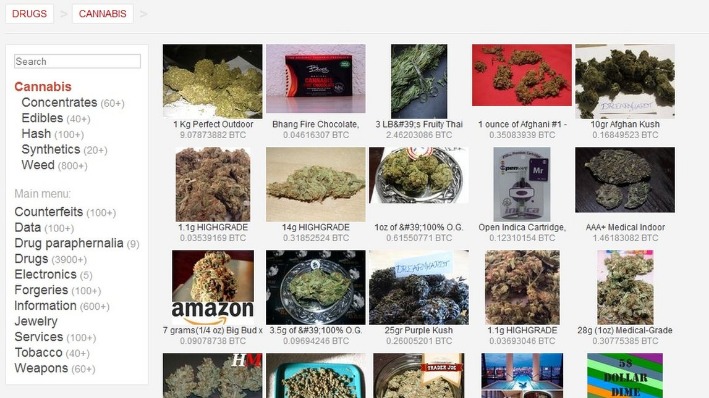
Now, that is not to say illegal behavior is completely beyond detection. The dark web combines encryption, anonymity, and hidden doorways to provide the perfect sanctuary for such illicit activity compared to the usual internet, which is more vulnerable and trackable. From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. Although these marketplaces are continuously shut down by law enforcement agencies, they still work today. Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they have better security than the older ones. Convert and track crypto rates for darknet marketplace transactions—stay ahead of the game.
DrugHub Market
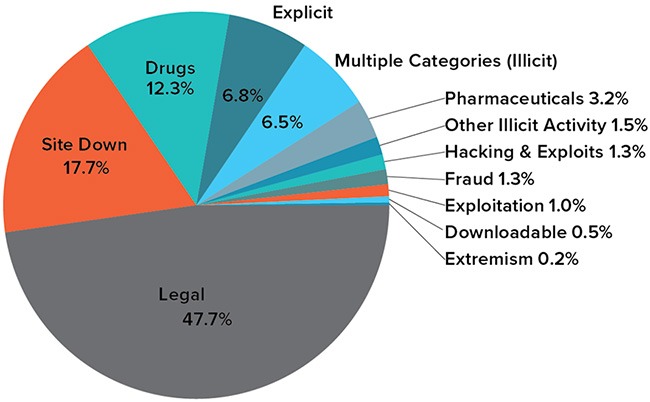
To achieve this, he leveraged Tor, a privacy-focused browser that masked users’ identities, along with Bitcoin for anonymous transactions. The dark web is a part of the internet that isn’t indexed by search engines. You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. Businesses must prioritize cybersecurity by implementing Dark Web scanning tools, strengthening access controls, and educating employees about emerging threats. Identifying security vulnerabilities before cybercriminals exploit them is essential for maintaining operational integrity.
Notes From The Dark Web: Analyzing Ukraine-Related Chatter In Key Forums
Darknets and dark markets have propelled the growth of cybercrime by offering a platform for the sale and exchange of malicious tools and services. Cybercriminals use these platforms to traffic in stolen data, execute targeted ransomware attacks, and collaborate on advanced hacking techniques. Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide. Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors.
Law enforcement shutdowns are also only one type of disruption that dark web communities face. Last week, one of the dark web’s most prominent drug marketplaces—Archetyp—was shut down in an international, multi-agency law enforcement operation following years of investigations. It was touted as a major policing win and was accompanied by a slick cyberpunk-themed video.

As the darknet continues to grow, its markets are expected to adopt even more sophisticated tools for secure trading, further enhancing the user experience and solidifying their role in modern commerce. Forums and magazines play a crucial role in keeping users informed about new market links and updates. Platforms like Dread and Darknet Live provide real-time discussions, vendor reviews, and security tips, ensuring users can navigate the darknet safely and efficiently. Table 3 shows the minimum password requirements of the twelve studied dark web markets.
Cryptocurrencies: The Financial Lifeline Of The Dark Web
Additionally, the implementation of decentralized marketplaces has further enhanced security by eliminating single points of failure. These advancements will further solidify their position as a secure and reliable option for users worldwide. The integration of cryptocurrencies like Bitcoin and Monero remains a cornerstone of these platforms. Bitcoin, with its widespread adoption, offers a balance between accessibility and security, while Monero provides enhanced privacy features, making it the preferred choice for users prioritizing anonymity.
An Increased Number Of Linux And Windows Users Are Encountering Exploits: Kaspersky Report
They showed various strategies designed by onion service operators to protect their users from phishing attacks. They also proposed “recognisers” capable of detecting phishing to fill the existing research gap. There are some parallels between these papers and the work we are presenting in the current paper here, but there are also several differences. For instance, our focus extends beyond security mechanisms specifically designed to prevent phishing attacks (though some are indeed effective against such attacks). We also cover mechanisms related to DDoS attacks, account, web and financial security, together with some other related topics. Georgoulias et al. 18 comprehensively documented the features and functionality of existing dark web markets in 2021.
Some marketplaces even offer dispute resolution mechanisms, mediating conflicts between buyers and vendors. Remember, however, that these measures aren’t foolproof, and inherent risks remain. The dark web marketplace landscape in 2024 is a diverse ecosystem, each platform boasting unique features and catering to specific clienteles. Hydra, a behemoth with millions of users, offered a vast array of products, from everyday items to illicit goods. White House Market, on the other hand, prided itself on high-quality drugs and a strict vendor vetting process, attracting a premium clientele. Other notable players included World Market, specializing in stolen data and hacking tools, and Tochka, catering to Russian speakers.
- Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft.
- Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web.
- We showed that a small fraction of traders is responsible for a large fraction of the trading volume, and by analysing the networks of buyers and sellers, we found different resilience regimes.
- As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring.
Exploring The Dark Web: Understanding Its Role In Cybersecurity Threats
The marketplace has a simple interface, lets users filter logs easily, and accepts Bitcoin, Monero, and Litecoin for payments. Plus, there’s a thorough vetting process for new buyers and sellers to keep the community more secure. In a way, it feels more like a private club than an open market, and that’s exactly how the operators want it.
With 25,000+ users and 3,000+ vendors, it’s the gold standard for escrow security and scale. First, we describe the security mechanisms used by dark web markets in web security. We walk through the process of accessing a marketplace to explore security mechanisms, and cover an open source software commonly used by the dark markets. Following this, we describe account security, which covers the username, password & PIN requirements, mnemonics, MFA and account kill-switch. Finally, we describe the details of their implementation of financial security, including the supported currencies, transaction types, as well as the handling of complaints and general user support.
Trading Tips
The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. The layers of encryption hide your data and activity from snooping eyes. These markets rely on encryption, escrow systems, and vendor ratings to function in a trustless environment.
Knowing how to spot a legitimate dark web marketplace can help protect your privacy and funds. Dark markets often employ end-to-end encryption for communication between buyers and sellers, enhancing security and privacy. This encryption ensures that messages cannot be intercepted and read by third parties, including law enforcement. The use of digital signatures can also help verify the authenticity of users and transactions.