While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Before Hidden Wiki is Daniel, a ‘dark web websites’ aggregator that can help you navigate the onion maze. Daniel acts as a dark web search engine to help users find reliable onion sites. Daniel regularly crawls the dark web searching for new websites or checking the status(es) of other websites.

Tor-Krypto-Wallets
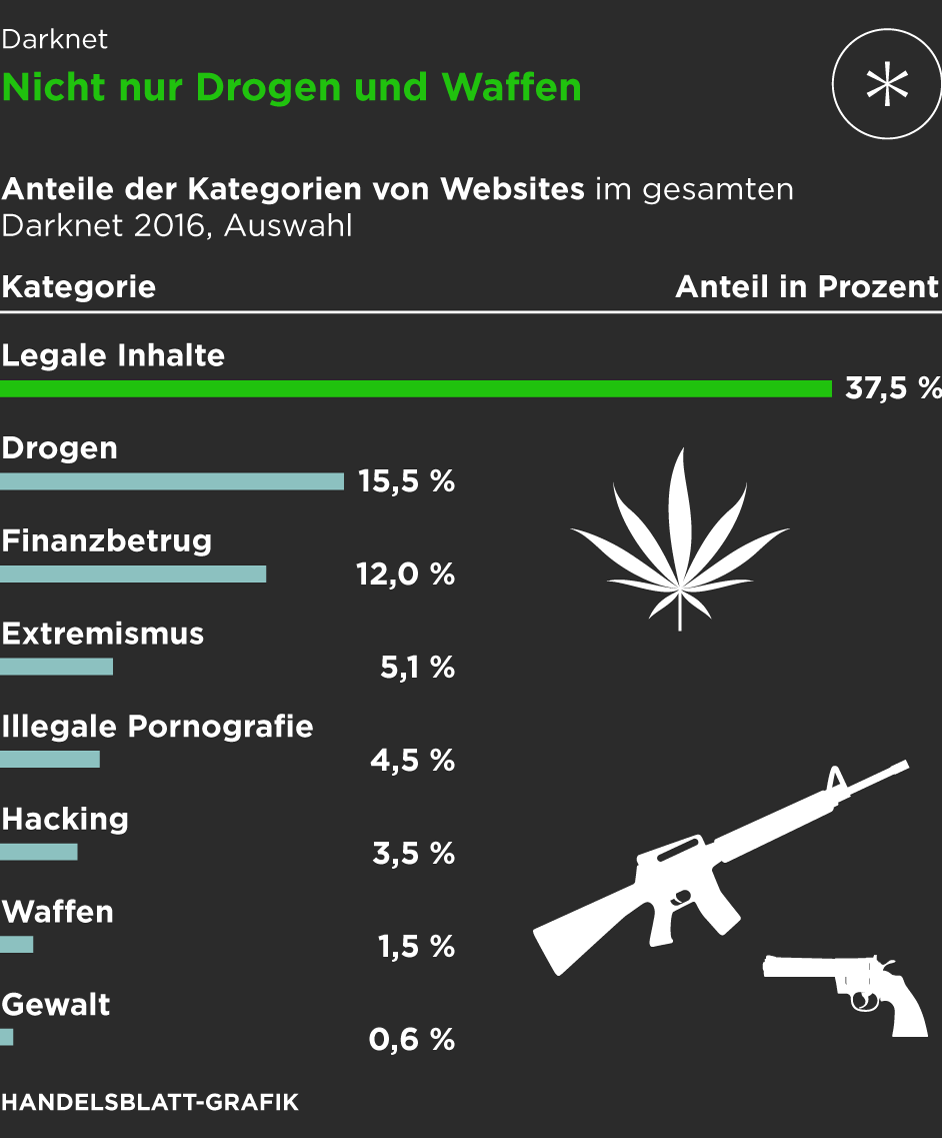
The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too. For example, you can find information unavailable to the public and share data privately while protecting your online identity.
Ist Es Sicher, Tor Für Alltägliches Surfen Zu Nutzen?
Though people usually think of dark websites as the wrong online place, that’s not the complete truth. Although the underground internet world is rife with everything bad, it also hosts positive elements. It then depends on you, as the user, how you surf the dark world. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide. This just involves turning on your VPN before you open Tor and connect to dark web sites.

Other Ways To Access Dark Web Platforms
In addition, you can connect your Keybase account with X, GitHub, or Reddit to let people easily trust that they are talking to the actual person. Also, the platform has a feature of automatic deletion of messages – set a timer and they will be deleted after a set period. The dark web version of Facebook isn’t malicious, but if you log into it, it will keep your data.
Die Beliebtesten Darknet Seiten
The site doesn’t require an email verification, though it offers all the features and security that you want in a dark web marketplace. Ahmia is a safe alternative search engine for users who prefer the dark web. It also provides insights, helpful statistics, and updates regarding the Tor network. Few countries operate with strict censorship on citizens’ internet access, preventing them from getting information in or out. BBC is the most popular news source and is the best example of restrictions on International media. This will help you to remain anonymous and secure at all Tor entry and exit nodes.
FAQ: More About Onion Sites

Criminals prefer the dark web because it offers anonymity like never before. But as long as you don’t knowingly engage in illicit activity on the dark web, you are completely fine. Lastly, to stay up-to-date with the happenings on a particular dark web website, forums are set up as a hub for information exchange. It can’t provide solutions should users encounter issues while using the website. Since privacy and security are a concern while using the dark web, the websites you visit must have the encryption necessary (HTTPS, preferably) to protect you.
Can You Be Traced On Tor?
- In some countries, evading government restrictions to seek new political ideologies is punishable.
- Other major news sources blocked in some countries, like the BBC, also have dark web versions.
- It is important to note that the people or journalists who use ProPublica to spread their truth recognize the risk of doing so.
- This website used to host over 7,000 onion sites, giving users access to many dark web links.
Read about the adventures of modern-day explorers who have made it their mission to venture into the tunnel network of huge American universities. The site is different from our whole list, but still worth a mention. The wallet is free, and since it’s open-source, anyone can inspect, verify, and contribute to the code.
- Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous.
- Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.
- The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin.
- For several years, Yahoo was at the apex as the internet’s best web service provider, offering…
- It is the dark web’s version of Wikipedia with a massive links directory.
Die Stille Gefahr In Ihrem Code: Sicherheitslücken Im Software Development Life Cycle (SDLC)
So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions.
Definitely yes, especially if this is your first time on the dark web. Hidden Wiki, although comprehensive, contains some very disturbing and very illegal info. TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity.
It does not store logs and is protected from interference and malicious attacks. The platform is free and is run by volunteers in the US who prefer privacy and security. Another standout feature is that the servers can’t see what you type, copy, paste, or send. To increase the security level, add password protection and determine the expiration time for messages.
Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. Blockchain even has an HTTPS security certificate for even better protection. The dark web and the deep web are often used interchangeably, but they’re two distinct concepts. A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites.

In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers.