
Simply complete a Bitcoin address search to view it on the blockchain. Plus, visit our Bitcoin Charts to see what’s happening in the industry. With the Tor browser launched or a Tor private window opened in Brave, you’re now connected to the darknet and ready to browse. Create an account with a username, password, and email and complete the captcha. If you already own bitcoin, or have obtained some using one of the methods described above, you can skip this section. Otherwise, here’s how to purchase your first BTC on Localcryptos.com.
A Quick Tour Of Dark Web Markets: The Internet’s Underbelly
It helps us stay more vigilant, better protect ourselves, and make informed decisions online. Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials. It supports operations in multiple languages and operates on both clearnet and Tor. DarkMarket also advertised itself as being the only such site administered exclusively by women.
Digital Goods
That way, they aim to create secure forums and limit outsiders like law enforcement. Likewise, law enforcement agencies each day continue to fine-tune their strategies to get past these networks. At KELA, we help you identify and mitigate risks by providing actionable intelligence from the darknet. Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services.
VPN (Virtual Private Network)
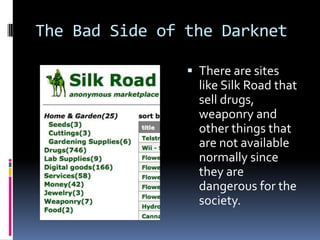
It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. The Torrez market is one of the biggest dark net marketplaces, also called a community-driven marketplace. It contains a good selection of product listings that range over 35,000 items.
Table Of Contents
One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud. Malicious vendors often infect buyers with spyware, ransomware, or infostealer malware hidden in downloadable files. Some listings are nothing more than scams designed to trick people into sending cryptocurrency without delivering anything in return.
Best Free Firewall Software In 2025
- They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.
- And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever.
- Exploring the Dark Web comes with inherent risks and potential dangers.
- The Dark Web is a hidden part of the internet that is not accessible through traditional search engines or web browsers.
- Let’s get this straight — not everything on the dark web is illegal or harmful.
- The vendors aren’t required to register or apply for a vendor account while using this platform.
A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience.
Top-10 Dark-Web Marketplaces In 2025: Overviews, Use-Cases, And Risks
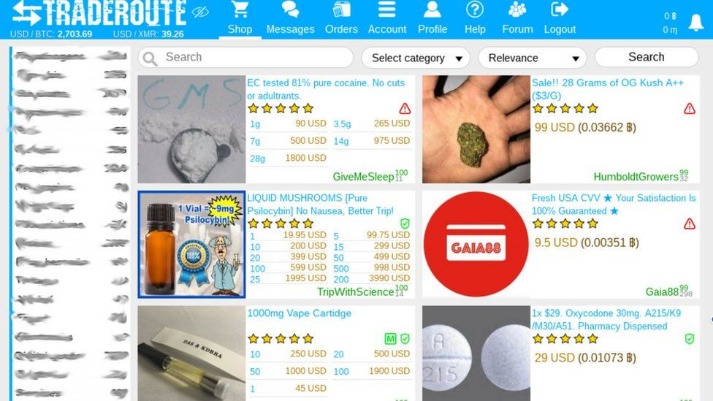
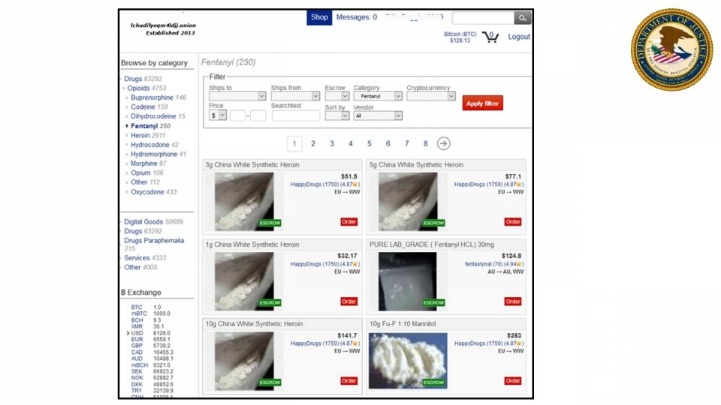
These hidden platforms have become breeding grounds for illegal activities, trading in everything from drugs and weapons to stolen data and hacking services. The allure of anonymity and untraceable transactions has attracted criminals from around the globe, making these marketplaces a constant source of concern for cybersecurity experts. But occasionally, he’ll ask a friend who already uses a darknet marketplace to get him something from there.
Also, while this huge portion of the internet has a reputation as home to nefarious activities like hacking and drug trafficking, it also harbors legitimate activities like journalists and whistleblowers. When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track. It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. Last September, another international police sting, Operation DisrupTor, announced the results of a push to catch drug dealers and other criminals who had used Wall Street Market. A hundred and seventy-nine people were arrested in seven countries, a hundred and twenty-one of them in the U.S.
In addition, several fake websites impersonate the famous dark net marketplace to obtain your financial and personal information and use it for malicious purposes. Just like ecommerce stores on the regular web, DNMs come and go and rise in fall in popularity. At the time of writing, Empire is the most popular darknet market, but is frequently offline for periods of time, making it hard to access.
Topics And Products Sold
However, it has since become a thriving hub for illegal activities, including drug trafficking, hacking, counterfeit goods, weapons sales, and even hiring hitmen. 🔹 Protect Your Business with CyberNodAt CyberNod, we provide comprehensive Dark Web scanning and cybersecurity assessments to help businesses identify and mitigate risks. Don’t wait for a security breach—conduct a Dark Web scan today to safeguard your data. Visit CyberNod and take the first step toward a secure digital future. A multi-layered cybersecurity strategy incorporating Dark Web monitoring, cybersecurity risk assessments, and employee training can significantly reduce vulnerabilities. Corporate espionage is a growing concern, with competitors and nation-state actors leveraging stolen data to gain unauthorized access to intellectual property, trade secrets, and financial records.
- The dark web is designed in such a manner that it hides the identities and locations of its visitors.
- By exploring the unique challenges posed by each platform, we aim to shed light on the strong security features of these top dark web markets.
- Some believe STYX is the OG darknet market when it comes to financial crimes.
- However, by combining Tor with Tails, which is a unique OS, we can increase our security and online safety.
- If you do need to access a dark web website for legitimate reasons, you can check directories like The Hidden Wiki to help find options.
Dark web directories, such as the “Hidden Wiki,” can direct you to authentic. But those directories may not be 100 percent reliable themselves, so take any information with a grain of salt. If you are new about dark web and do not know how to install tor click here.
Ulbricht’s hefty prison sentence did not appear to have the intended deterrent effect. Multiple markets emerged to fill the void and, in doing so, created a thriving ecosystem profiting from stolen personal data. For instance, a factory employee can secretly slip away with one and sell it on the darknet markets.
But the dark web also offers drug traffickers cover from police surveillance. In a recent scan of the site, Dream featured roughly 1,000 listings for drugs that ship within Canada, ranging from opium, morphine and fentanyl to ecstasy, ketamine and date-rape drugs. A screenshot of Dream Market, below, shows drugs on offer, including crystal meth, cocaine, hash and MDMA.



