The leading darknet markets in 2025 offer a wide range of substances, catering to various preferences and needs. This diversity not only attracts a larger user base but also fosters competition among vendors, driving innovation and quality improvement. Buyers benefit from access to a broader selection, ensuring they can find exactly what they are looking for. The leading markets offer a wide range of substances, from pharmaceuticals to recreational drugs, catering to various preferences. Detailed product descriptions, including purity levels and dosage information, help buyers make informed decisions.
Onion Links: How To Access Them
Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds. Internet traffic first passes through the Tor Network, and then through the VPN. This means the VPN provider doesn’t see your real IP address and the VPN protects you from those bad exit nodes.
Cryptocurrency Transactions
- While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity.
- Fraud-related products, consumer electronicselectronics, self-defense products, and even hosting.
- A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation.
- Darknet markets provide a secure platform for trading various goods, including pharmaceuticals and digital products.
- It will offer you an additional layer of encryption to access the deep parts of the internet.
However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address.
Secure Your Cryptocurrency Transactions
For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero.
Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI. The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites.
The Dark Web Market Onion – Exploring The Hidden Depths Of The Internet’s Underworld
Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019.
Easy – Extremely Simple How To Use Monero (Video Tutorial)
As darknet markets continue to evolve, they are expected to offer even more sophisticated tools and features, further enhancing their appeal to users. The focus on security, privacy, and efficiency ensures that these platforms remain the go-to choice for individuals seeking a reliable and discreet way to engage in drug trade. Aside from physical products, dark web markets also host the sale of digital goods and services. These can include stolen credit card information, hacking services, identity theft kits, and various digital products like software licenses, accounts, and databases. In order to access dark web markets, you’ll need to use a special browser called Tor (The Onion Router), which allows you to browse anonymously and access websites with .onion links.
Besides this, it supports wallet-less transactions and accepts payments through Bitcoins, Litecoin, Monero, and Zcash. However, you must wait some time to reassess this marketplace because it’s been shut down. It issued a press release revealing that, from December 2021, the website won’t be functional anymore. The website looks organized and has a clean, sleek, easy-to-use UI. You can find featured listings on the homepage and browse the products of your choice. There’s also a search bar that you can use to search for any particular product or vendor.
How TOR Protects Anonymity

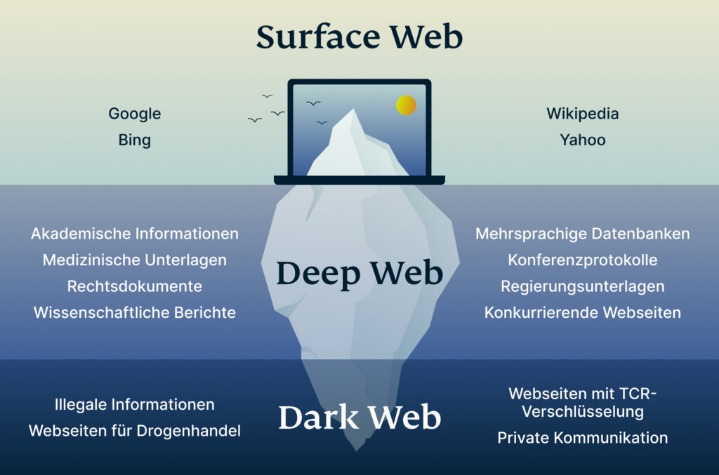
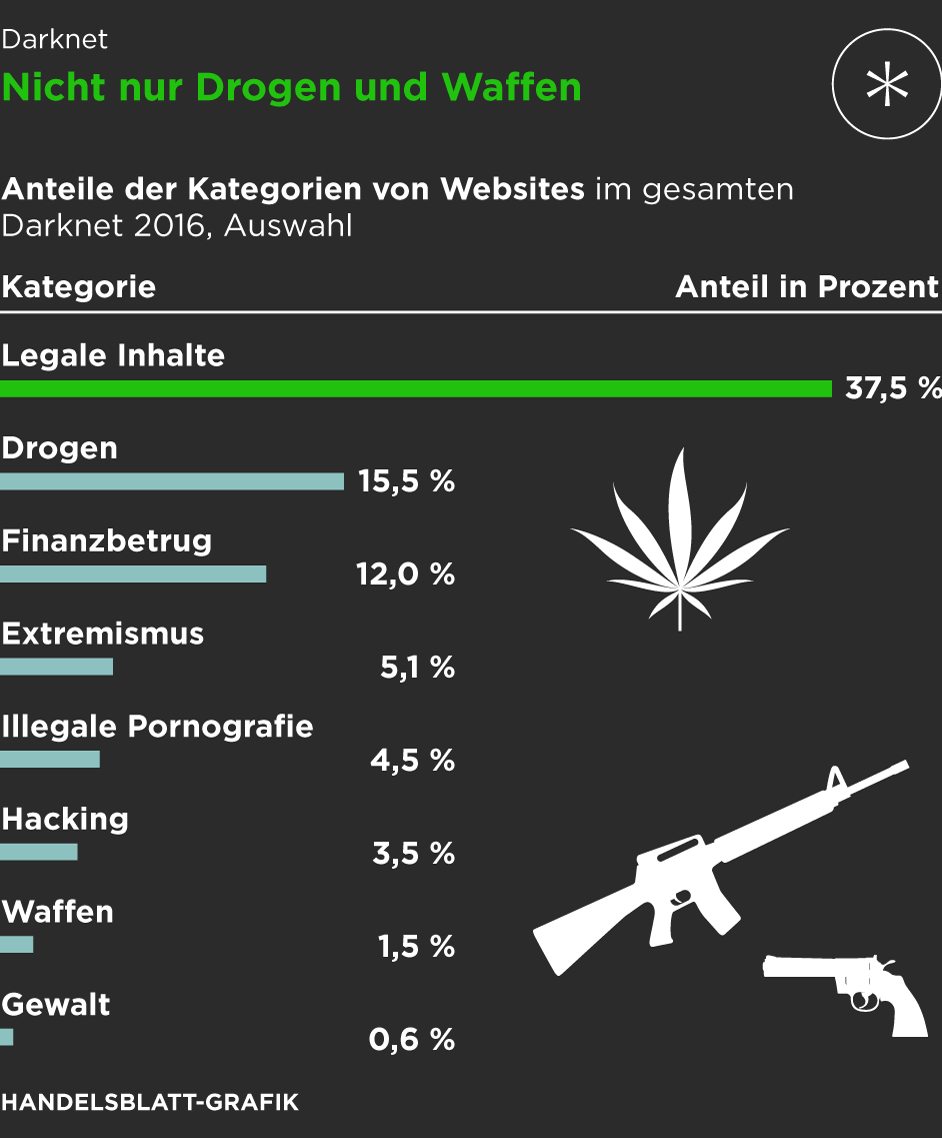
While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online. In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information. Tools like Tor are used to bypass government-imposed firewalls and surveillance, ensuring open communication. The significance here is the preservation of civil liberties and the right to information.
Some users may utilize these platforms to access information or services that are not easily available through traditional channels. However, it is still essential to exercise caution and carefully evaluate the legitimacy and ethical implications of any transaction. One of the main risks when navigating the dark web is encountering scams and fraudulent sellers. Since these markets operate outside the law, there is no guarantee that the products or services offered are legitimate or safe.
In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described. Once the buyer confirms satisfaction, the funds are released to the seller. Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support. These features help create a sense of ‘trust’ among users, even in the criminal ecosystem.

These .onion links are the key to accessing the dark web, as they are the unique URLs of deep web marketplaces. Unlike regular URLs, dark web market URLs are structured in a way that ensures anonymity and encryption, making it extremely difficult for authorities to trace the activities taking place. The darknet is used for anonymous communication, accessing censored information, and protecting privacy. Journalists and activists use it to communicate securely in oppressive regimes.
If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites. Unlike other search engines, it does not collect or share web activities and personal data of users. Unlike Tor, however, it cannot be used to access the public internet. It can only be used to access hidden services specific to the I2P network.
One of the things STYX is infamous for is having a rigorous verification process for users that makes it seem more exclusive. They even have a Telegram channel to provide their clients with live updates. Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace. Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries. It is similar to an online store, except it’s not the type you’ll find with a quick Google search. Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it.
- The use of escrow systems ensures that funds are only released once the buyer confirms receipt of the product, reducing the risk of fraud and increasing trust between parties.
- A lot of vendors from all over the world are registered here, offering an extensive range of products, including digital services, security tools, and other equipment.
- For safer browsing, it is highly recommended to also use a VPN and antivirus software.
- As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals.
- Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P.
The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions.