He was arrested in a San Francisco library while logged in as site admin. For those venturing to the shadier side of the web or those who just want to know their identity is safe, dark web monitoring tools and identity theft protection are a must-have. Throughout this guide, we’ve explored the legal and ethical considerations of venturing into the dark web, how to enhance security and anonymity, and the criteria for identifying trustworthy resources.
Additionally, PhantomX employs a decentralized hosting model, making it resistant to takedowns and ensuring continuous availability. A VPN protects your connection against everyone, not just your ISP and the authorities. It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information.
Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials. It supports operations in multiple languages and operates on both clearnet and Tor. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. Always use a fake name and a temporary email address when you buy something from the dark net shops. You can even use a secure email provider or a burner email address whenever you visit the dark web.
I Legal And Ethical Considerations

In fact, some parts of it actually provide a safe space for privacy and freedom, especially where traditional internet access is limited or censored. One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud. Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach. Criminals use this information for money laundering, opening bank accounts, applying for loans, and draining your finances.
- It is a relatively new provider but offers better features than most established VPNs.
- These sites provide a level of privacy and anonymity unavailable on the surface web, offering content and goods that cannot be easily found through traditional online platforms.
- For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web.
- Its free plan comes with up to 1 GB of storage, 150 messages per day, and 1 email address.
- DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links.
- But if you still decide to access these websites, for education or research purposes, make sure you stay cautious.
Secure Your Connection
Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. Significant technological innovations and trends have reshaped dark-web marketplaces over recent years.
Onion sites can be safe in terms of privacy protection due to strong encryption, but they also host a significant amount of illegal content and scams. It’s important to only visit trusted sites and avoid clicking on suspicious links. Everything is in English, but users from around the world are welcome.
In 2025, many platforms have adopted decentralized architectures, reducing single points of failure that previously made them vulnerable to law enforcement takedowns. TRM provides blockchain intelligence to help financial institutions, cryptocurrency businesses, and public agencies detect, investigate, and manage crypto-related fraud and financial crime. TRM’s risk management platform includes solutions for transaction monitoring and wallet screening, entity risk scoring – including VASP due diligence – and source and destination of funds tracing.
Can You Access The Dark Web With A VPN?
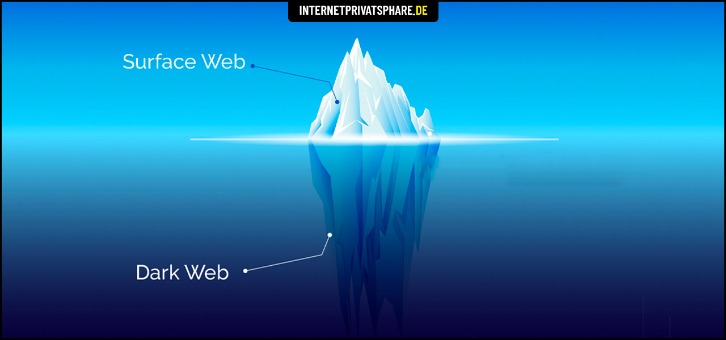
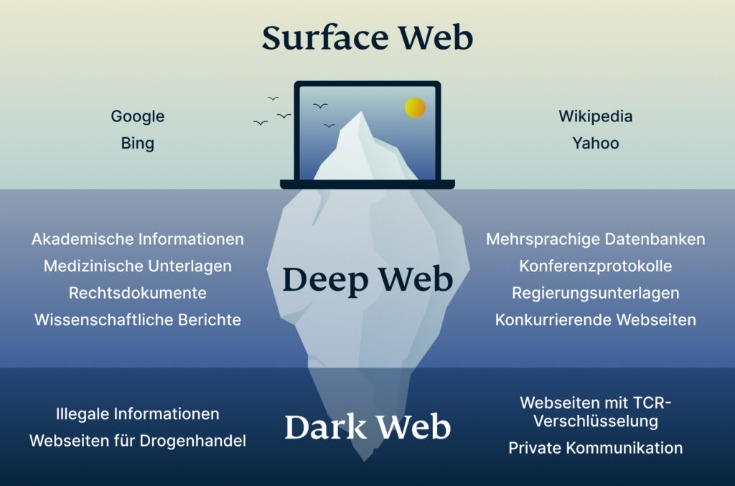
To look at it in a different way, it makes up between 90% and 95% of the internet. The dark web and the deep web are often used interchangeably, but they’re two distinct concepts. Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps.
Hacking Services
If you wish to access the snapshots of these websites, just type in the domain name, and you will get the results depending on how many records exist on the website. This is a great resource for users looking to refer to old prices or job listings that have changed or are outdated. It saves a select version of each page and preserves it even after upgrades have taken effect on the original site. However, not all books on this site are legally available, so they don’t have copyrights. That means you may violate copyright laws while downloading books, so use a VPN to protect yourself from any legal repercussions if you have a dire need to use it.
Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails. Still, since they exist within the dark web, there is a high chance that malicious entities have co-opted one or more for illegal activities.
A Persistent Trade
I’ve used it a few times, and it’s never let me down—great for folks who like their dark web with a modern twist. If you’re curious about what’s going on in the dark web next year, you’re in the right place. I’ve been digging into marketplaces like Abacus and AlphaBay for a while now, and this page breaks down what’s hot in 2025. You’ll find reviews, quick tables with the nitty-gritty details, and some practical tips on using Monero (see how) or setting up PGP (check it out). Plus, we’ve got some fresh takes on dark web trends and how to get started.
How Darknet Market Lists Enhance Secure Drug Trade
- Dedicated support teams and automated systems help resolve issues quickly, ensuring a smooth experience for all users.
- It’s for the good that these sites are not available for the general internet user.
- If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection.
- There are thousands of websites on the dark web, many—but not all—of which are illicit marketplaces selling stolen personal data.
- A VPN provides strong security for everyday browsing without the extra delays, middle checkpoint, and then finally the exit gate.
Buyers won’t come to the site if there’s nothing to buy, and sellers won’t come to the site if there’s no one to buy their products. Server admins will have to either make special agreements to get initial sellers on board, or supply products themselves to get things started. One of the central76 discussion forums was Reddit’s /r/DarkNetMarkets/,777879 which has been the subject of legal investigation, as well as the Tor-based discussion forum, The Hub.
Join millions of users who trust ForestVPN for privacy and unrestricted internet access. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable.
Best VPNs For Staying Safe And Anonymous On The Dark Web In 2025
Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. If you only want to mask your IP address and don’t need to access the dark web, then going online with a VPN is much easier and faster than using Tor. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way.

Accessing the dark web is legal in itself; the nature of the activities you engage in ensures it stays that way. Criminals prefer the dark web because it offers anonymity like never before. But as long as you don’t knowingly engage in illicit activity on the dark web, you are completely fine. This browser is the most suitable option for accessing the dark web, thanks to its multiple layers of encryption. Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden.