
Downloading files from the Tor browser can compromise your anonymity. Malicious files might bypass Tor’s security, giving away your real IP address. If you must download files, ensure you’re using a separate, secure environment — such as a virtual machine. Always run the latest version of the Tor Browser to protect against security vulnerabilities.
Privacy Tools And Services
Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions.
Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. For several years, Yahoo was at the apex as the internet’s best web service provider, offering… In today’s digital era, where information is constantly on the move across all digital platforms, an… If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic.
- Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky.
- There’s a wealth of legitimate resources and communities hidden behind the “.onion” domain, waiting to be explored by those who dare.
- Additionally, we provide detailed descriptions and safety advice for each link, empowering users to make informed decisions.
- To access them, copy and paste the hyperlinks provided into the Tor browser.
- Even with the increase in law enforcement pressure, the dark web market still achieved a revenue of $2 billion in 2024.
- Always access the Hidden Wiki through the official Tor Browser, never via a standard browser.
Q: I Sent My Bitcoin To The Address But It Isn’t Showing Up What’s Happening?
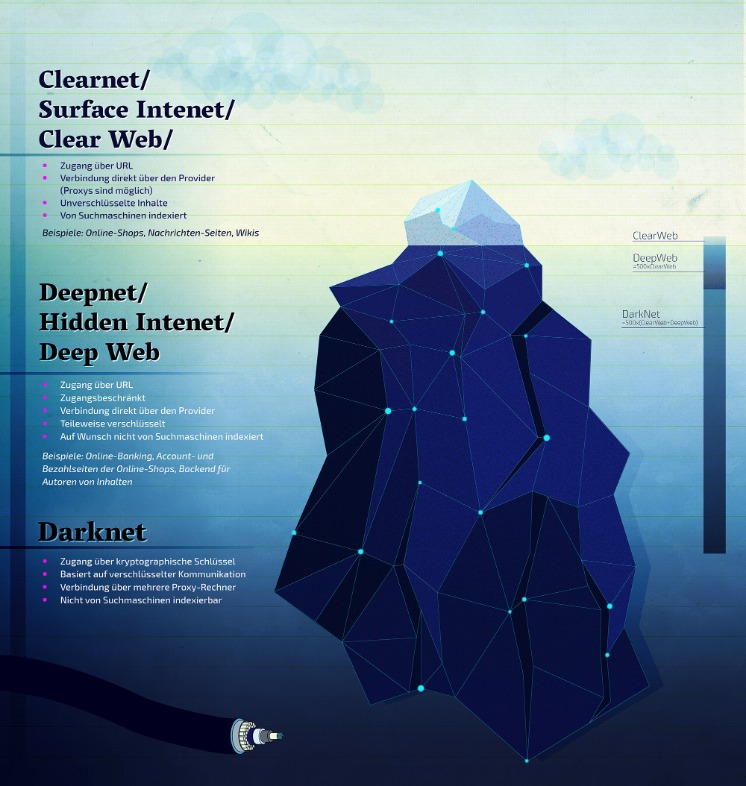
The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means. So, what even is this dark web, and why are these marketplaces present there? This section can also touch on mirror sites — what they are, why they exist, and how users identify trustworthy mirrors. He recommends verifying market employees carefully, and to weed out law enforcement infiltration through barium meal tests. Even platforms like Netflix, which require paid access, are technically part of the Deep Web. You’re only scratching the surface when you use the Internet for daily activities—reading news, managing finances, running businesses.
Cryptocurrency Services

To understand the dark web is to embark upon a journey through its historical milestones. To help you make educated choices about cybersecurity to keep you (and your data) safe and secure, by providing detailed, accurate, and practical information based on thorough testing. Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage.
More Hidden Sites
OnionName lets you generate an .onion domain name that starts with a specific keyword — like onionamev33r7w4zckyttobq3vrt725iuyr6xessihxifhxrhupixqad.onion/, which is OnionName’s dark web link. The keyword in that example is “onioname,” which is right at the start of the .onion link. With a readable site name like that, people will know what to expect when they click on the link. Darknetlive contains articles about everything related to the dark web. Articles are published regularly and include interesting information, images, and quotes from officials. This way, if you’re interested in a specific topic, you can find it quickly.
Other Privacy Tools And Services
This is because law enforcement often actively monitors these sites. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. All in all, it is not illegal to access the dark web, but it can create issues for you. If you don’t take the necessary measures, many unsavory activities can expose you to unnecessary risks. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator.
How The Hidden Wiki Became The Gateway To The Dark Web
Of course, this only works if the surfer does not enter any personal data during the session — for example, if they do not log in to Facebook or their email inbox. The darknet is primarily used to communicate unrecognized on the internet. Anonymization services prevent your own internet activities from being spied on.
How To Find New, Active Dark Web Links
“Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below. No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet.

Why The Hidden Wiki Remains Important
Users can ask questions, share answers, and engage in discussions without revealing their identities. It’s maintained by a volunteer-run collective from the USA that protects the platform from malicious attacks and pledges to support social justice and progressive causes. Riseup’s secure email and chat help individuals communicate without fear of surveillance or data interception.
Dark.fail has become one of the most trusted alternatives to the traditional Hidden Wiki. This directory focuses on providing users with verified, frequently updated links to a broad range of dark web services, including marketplaces, forums, and whistleblower platforms. Its community-driven verification system helps minimize the risk of scams and outdated URLs.
The lack of regulation leaves the dark web rife with offensive content and unsafe websites. Tor Metrics is a set of tools and data provided by the Tor Project that offers insights into the performance, usage, and activity of the Tor ecosystem and its nodes. Besides monitoring and improving the network, the data can be used to detect possible censorship or attacks. Due to the privacy-forward ethos of the Tor project, Tor Metrics stresses that the data it collects must not undermine the anonymity or security of the network. ProtonMail is a Swiss-based encrypted email service that doesn’t require personal information when you sign up.
Deep Web Search Engines (Onion Links
To do that, you’ll need a dark web search engine like Torch or Ahmia. SecureDrop is an anonymous file-sharing platform designed for secure communication between whistleblowers and journalists. While anyone can use it, it’s built for high-stakes exchanges, making it overkill for routine file sharing or data backups.
Torch is one of the oldest dark web search engines, having served the darknet community for years. It boasts a vast archive of over 400,000 pages, providing comprehensive coverage of .onion sites, including forums, blogs, and marketplaces. The darknet version of DuckDuckGo is not a search engine for the dark web, but a private browsing tool for the dark web. DuckDuckGo’s regular site can take you to the dark web, as it brings up onion sites and dark web links when searched. Neither DuckDuckGo’s dark nor normal versions keep a log of your web activity.



