Yes, you definitely need a VPN if you want to access the dark web on your phone. This is because the dark web is full of potentially dangerous content, and a VPN will help keep your identity and personal information safe. Without a VPN, you could be putting yourself at risk of being hacked or scammed.
- We may just have heard of the Dark Web if you are a curious person to seek to explore the depths of the Internet.
- This “onion” routing masks your IP address and encrypts your data multiple times, peeling away layers of encryption at each relay.
- This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting.
- Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent.
- While this market started in Canada in 2021, WeTheNorth now sells to both Canadian and international users.
- A VPN contains security features that obfuscate your location and hide your IP address from anyone who may be snooping around your online traffic.
I2P (Invisible Internet Project)
Though Dream Market is no longer operational, its influence on the dark web marketplace continues. The shutdown of the site marked a turning point, and its closure led many to rethink their strategies for accessing these underground platforms. Despite the rise of other markets, the absence of Dream Market has left a gap that has yet to be filled entirely. All darknet markets use escrow this basically means the buyer’s payment is held in escrow until the buyer confirms they’ve received the product which gives a piece of mind to the buyer. They also use 2FA, PGP, Private Mirros and Multi Signature to name some of the security features. For those who want to explore darknet markets while staying informed we are your one stop shop.

Disadvantages Of The Tor Browser
Focusing on privacy and security, MGM supports transactions in Bitcoin (BTC) and Monero (XMR), and utilizes a direct payment system for each purchase, appealing to users who value privacy. Everything is in English, but users from around the world are welcome. You’ll get stolen credit cards, remote desktop account info, personal details, and various logs. What makes this market popular is the fact that it’s less expensive compared to the rest. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data. You should also consider freezing your credit to prevent identity theft.
Conclusion: Access The Dark Web Safely And Responsibly
A logless VPN, which doesn’t store any traffic logs nor session logs is highly preferable. Traffic logs are a bigger concern than session logs, but neither are good. You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions. If you plan to purchase on a dark net marketplace or dark web commerce sites, you’ll need to create a fake identity. Remember only to make purchases using digital currencies and never provide any online banking login details. The dark web is a section of the Internet not searchable through traditional search engines, where privacy and anonymity reign.
Go Only With Cryptocurrencies For Transactions
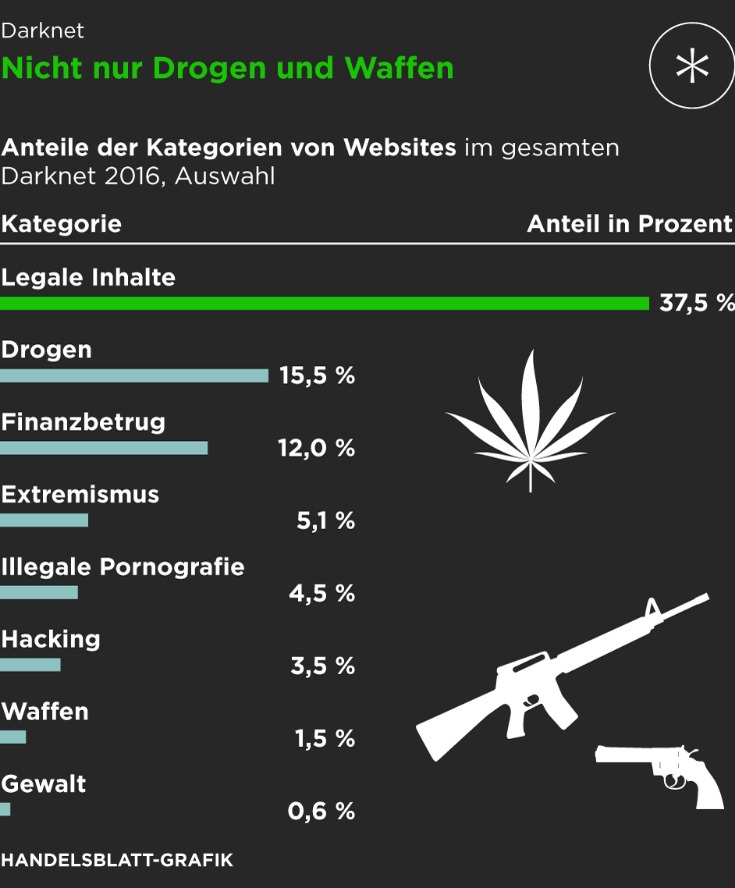
So, if a “business opportunity” sounds too perfect, it probably is. Some sellers offer cracked versions of expensive software that you’d typically pay hundreds of dollars for. Others sell pirated eBooks, academic materials, and entire premium courses ripped straight from paid platforms. Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content. The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims. Such content fuels a dangerous cycle of abuse, violence, and exploitation.

Step 3: Connect To The Tor Network
Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project.
- ZDNET tested the best VPNs available based on speed, number of servers, security features, price, and more.
- You can never be sure who’s really behind the other end of the line.
- That information can include checking and credit card account numbers, social security numbers, and other sensitive information.
- For your optimum dark web safety, you should ensure that once you’re done browsing the Darknet, shut all the browser windows as well as any other content that could be connected.
How To Access
If your information has been compromised, then it’s likely that your phone number is also on the dark web. Setting up I2P requires more configuration on the user’s part than Tor. I2P must be downloaded and installed, after which configuration is done through the router console.
By understanding the hazards you may face in the Dark Web and implementing the precautions outlined above, you’ll be better equipped to minimize your exposure to scams, malware, and identity risks. Remember that good judgment, ongoing education, and constant vigilance are your most powerful tools for maintaining a safe and private Dark Web experience. I2P is an anonymous overlay network designed primarily for peer-to-peer applications.
In this article, we’ll explain how these markets work, how you can keep up with changes in the darknet markets world. Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents. The significance lies in the potential compromise of national security. Governments and businesses must invest in advanced threat intelligence, cyber defense, and counter-espionage measures. To reduce the risk of fraud, many dark markets offer escrow services.
Other Collection Links:
Want to get illegal drugs, fake passports, Trojan, or other cyber attack software? Plus, there’s a thorough vetting process for new buyers and sellers to keep the community more secure. In a way, it feels more like a private club than an open market, and that’s exactly how the operators want it. That’s why they’re often a popular means of communication among activists, whistleblowers, political organizers, and ethical hackers. Of course, cybercriminals can also use them for nefarious purposes like discussing illegally shared interests, conspiring to commit crimes, or posting content deemed too unsavory for the clear web. Dark web forums typically look like run-of-the-mill message boards.

Hacker services against banks and other financial institutions are offered there. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes. The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito.
Le Roux was a talented programmer who turned into a deadly drug lord. What made his character interesting was using the dark web to build a powerful and ruthless cartel that survived law enforcement onslaught for years. Tor, for example, uses multi-layered encryption to create anonymous communication over a computer network.



