Buyers, also known as “carders,” typically will then turn around and use the data to clone a card or multiple cards, which can then be used to make illegal bulk online purchases that can be re-sold for a net profit. In the ever-evolving landscape of cyber threats, businesses face not only financial losses but also significant reputational damage when targeted by fraud actors on the dark web. Monitoring the deep and dark web becomes imperative for proactive defense against such threats.
What Form Of Fraud Or Theft Signals Credit Card Dumping?
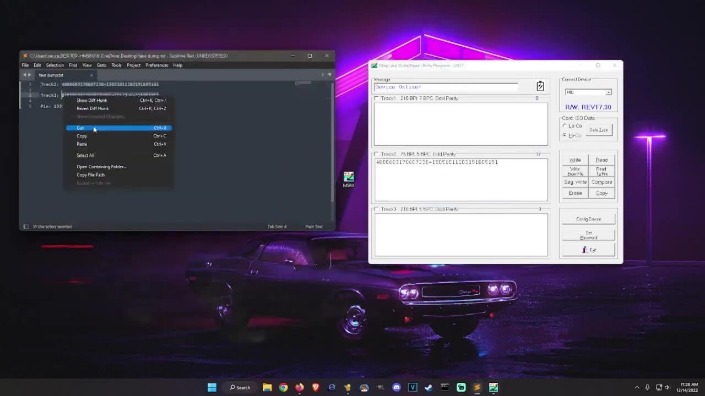
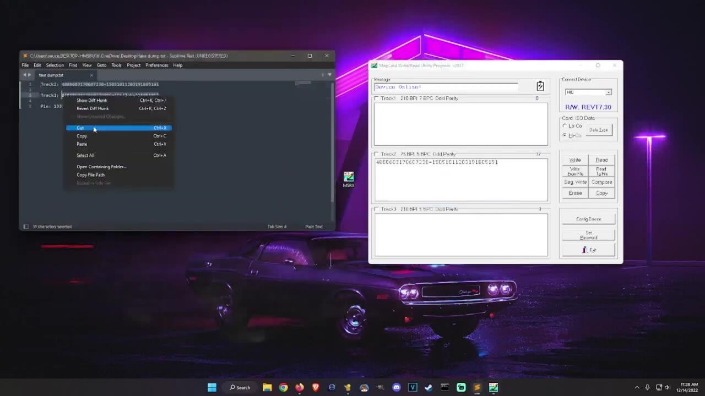
Recently, on February 17, 2025, Dark Web Informer claimed that B1ack’s Stash is a “legitimate” fraud site. Other sellers offer discounts for buying multiple cards, while the cheapest card — with between US$700 and US$1,000 on it — can cost as little as US$80. The best way to monitor your credit cards is by downloading your credit card company’s app from the Apple App Store and Google Play Store. BidenCash apparently used the free stolen data dump to draw attention for marketing, even using an image of President Biden as its brand identity, as discovered by Cyble researchers who detected the data breach. Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites.
Stolen Credit Cards Hit Dark Web For Free
Cybercriminals use cryptocurrency to buy and sell stolen card data anonymously. The stolen information is then used to make unauthorized online purchases using stolen credit cards, or resold on the black market. Operators behind the popular dark web carding market ‘BidenCash’ have released a dump of 1,221,551 credit cards to promote their underground payment card shop. Multiple security firms, noticed the promotional activity, but the news was first reported by threat intelligence firm Cyble and the Italian firm D3Lab. Carders tend to target specific sites that don’t have VBV or other protections against fraud. For fledgling criminals who don’t know how to use stolen credit cards, there are plenty of free and paid tutorials for carding on the dark web.
Exploring Benefits And Risks Of Using Credit Cards Or Card

Regardless of the type, engaging in or participating in credit card dumping activities is illegal, and individuals found doing so can face severe legal consequences. In recent years, I’ve observed some shifts in how carding is carried out—changes that mirror broader developments in both technology and threat intelligence research. Notably, cryptocurrency has become a valid option for carding operations, whether through exploiting stolen crypto wallets and accounts or using stolen credit card details to purchase cryptocurrency.
Can I Buy Bitcoin With A Credit Or Debit Card?
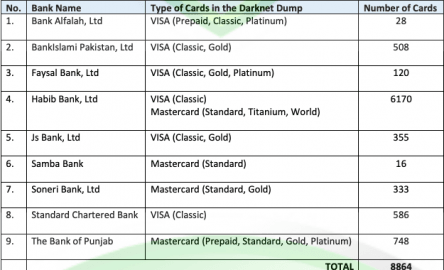
While it shares a similar purpose with Joker’s Stash, there is no confirmed connection between the two. Joker’s Stash was one of the largest and most infamous dark web carding marketplaces, operating from around 2014 until it voluntarily shut down in early 2021. It was known for selling high-quality stolen payment card details and used blockchain-based domains to evade law enforcement. The closure of Joker’s Stash left a gap in the cybercriminal ecosystem, which was later filled by other marketplaces. Our investigation into the activities of b1ack’s Stash has unveiled a substantial threat to the security of payment card data across local banks.
Impact On Financial Institutions And Customers
Multiple new shops, including BidenCash, appeared after UniCC, the initial new market leader, fell to a Russian crackdown in January 2022. AllWorld.Cards took a similar approach in August 2021, leaking details for more than 1 million cards obtained from 2018 to 2019. Transactions are conducted anonymously and encrypted, making it difficult for law enforcement to track down the criminals involved. In 2020, the average cost of a data breach was $3.86 million, according to a study by IBM. The consumer watchdog has been flooded with Optus-related scam complaints following the data breach. These generated numbers link to your real card but can be limited by merchant, amount, or time.
Credit card fraud on the dark web operates quite differently from what many people imagine. Owners of the best graphics cards made by AMD, rejoice — it seems that there could be a big performance boost coming your way. AMD has accidentally leaked the source code for its proprietary upscaling tech, FSR 4. Industries have already adopted it, and the biggest AI companies are racing to put it in the hands of students through exclusive deals and discounts. Now, it seems the next avenue is giving universal access to all citizens, starting with ChatGPT Plus.
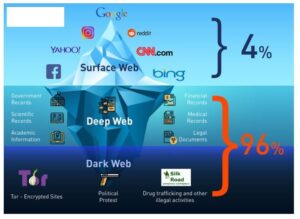
The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. Russian Market is considered to be one of the most popular, reliable, and valuable marketplaces. Unlike the name implies, Russian Market operates in English and doesn’t necessarily have a link to Russia or Russian speakers.
Dark Web Monitoring
Network segmentation is absolutely critical for businesses handling card data. Financial institutions tighten their security measures to prevent fraud but that also prevents legitimate transactions as a result. They invest massive resources into fraud detection systems, customer service teams dedicated to handling compromised cards, and the logistical nightmare of card reissuance. The pricing varies based on the card type, with premium cards from certain banks fetching higher prices. Rather than individual hackers working alone, the reality is that we’re dealing with sophisticated criminal enterprises that function like businesses, complete with customer service and quality guarantees.
AI Firm Says Its Technology Weaponised By Hackers
This not only protects against financial losses but also reinforces customer trust. In addition to just selling credit card details, some threat actors offer a “complete package” often referred to as “Fullz”. Fullz includes full personal details as well as financial details such as bank account details or social security numbers, which can be used for a full account takeover or identity theft. Card data on the dark web is a valuable commodity, and it’s often sold on specialized marketplaces known as Card Shops. These platforms are hubs for cybercriminals to buy and sell compromised payment card details. In conclusion, credit card dumps represent a significant threat to consumers and companies alike.
- If you believe your credit card information has been compromised, contact the credit card company immediately to cancel your credit card and outline unauthorized charges.
- Delta Dental of California (DDC), Delta Dental Insurance Company, Delta Dental of Pennsylvania, and other subsidiaries may have exposed data; the compromised data is not a product of the organizations.
- Criminals obtain this data through various methods, such as skimming or hacking into payment systems.
- They sell the information in various forms, such as individual card numbers, cardholder details, or entire databases, depending on the demand and price range.
- Buyers, also known as “carders,” typically will then turn around and use the data to clone a card or multiple cards, which can then be used to make illegal bulk online purchases that can be re-sold for a net profit.
Darknet Marketplace Snapshot Series: B1ack’s Stash
This involves adding daily listings of stolen credit card details to the site and periodically dumping large amounts of stolen credit card details at the same time. Deep and dark web credit card sites include forums and marketplaces that host the trade and share of illicit content relating to credit cards. According to a blog by SOCRadar, the release of such comprehensive data poses significant risks, including financial fraud and identity theft. This data enables cybercriminals to commit fraud, resell stolen credentials, and facilitate identity theft. If you suspect that your credit card information has been stolen through a data breach, contact your credit card issuer immediately and request a new card with a new account number.
This stolen information is then used to create counterfeit credit cards or make fraudulent online purchases. The term “dump” refers to the act of extracting the data from the credit card’s magnetic strip or chip. The supply chain for carding stores like Joker relies on large data breaches, usually sourced from hacks involving point-of-sale software for large retail or merchandise outlets.