
Financial literacy, regular account monitoring, secure online behaviors, and utilizing advanced protection methods such as two-factor authentication and virtual cards are essential strategies. Moreover, being alert to signs of card compromise and knowing how to respond swiftly if your data is stolen can drastically limit potential damage. Convicted individuals often face imprisonment ranging from one to ten years, alongside significant monetary fines and confiscation of illegal gains.
Why Do Carders Use Bots To Conduct Carding Attacks?
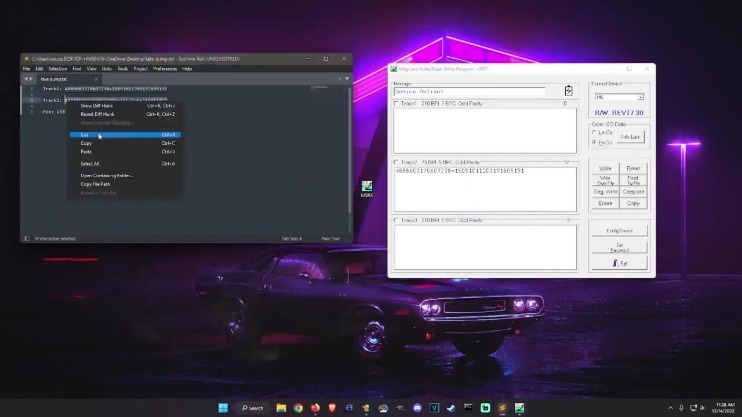
Once the carder has the necessary data, they can either use it themselves or sell it on carding forums to other interested parties. Carding involves the use of stolen credit card details to make fraudulent transactions. The information may be obtained through various means, such as hacking, phishing, skimming devices, or purchasing data from other criminals.
Despite significant disruptions, including a major hack in 2016, Nulled has maintained its status as a key player in the cybercriminal ecosystem. Forums provide a marketplace for buying and selling stolen data, including credit card information, personal identities, and login credentials. Post the dismantling of Joker’s Stash, cybercriminals displayed adaptability by establishing new marketplaces to fill the void, highlighting the resilience of criminal enterprises. This adaptability underscores the ongoing challenge faced by financial institutions in combating the ever-evolving threat of dark web credit card marketplaces.
Transaction Fraud How To Protect Your Business & Customers

They offer stolen credit card data, often organised by specific details like type or country, as well as carding tools such as bots and malware that help automate fraud. These marketplaces also provide related services such as credit card validation, cash-out assistance, and fake ID creation. Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details. These platforms continuously scour the deep and dark web, looking for any traces of your sensitive information.
The Top 7 Dark Web Marketplaces In 2025
This ensures that messages, transactions, and data exchanges remain confidential and protected from interception. Founded in 2005, Exploit is a leading Russian hacker forum operating on both TOR and the surface web. It connects cybercriminals with collaborators for hacking, fraud, and RaaS activities. Its structured organization and membership policies project professionalism, attracting genuine content and marginalizing non-Russian speakers. To conceal their true identities and locations, carders often employ proxy services.
Get Cybersecurity News, Insights, & Intelligence Straight To Your Inbox
It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures. Understanding the reasons behind their popularity can help cybersecurity engineers to develop more effective strategies to combat these digital threats. Most forum users operate under pseudonyms, further protecting their real identities. This anonymity encourages open communication and the sharing of sensitive information without fear of exposure.
- Here, you’ll find threads and detailed discussions on Socks, cardable websites, anonymity, VPNs, operating systems, hacked accounts, databases etc.
- Inform your bank or credit card issuer immediately to freeze your accounts and prevent further unauthorized transactions.
- Buyers, also known as “carders,” typically will then turn around and use the data to clone a card or multiple cards, which can then be used to make illegal bulk online purchases that can be re-sold for a net profit.
- Once in possession of valid card data, carders quickly use it to make fraudulent purchases online.
- LeakBase’s vibrant community and administrative team fuel its prominence in the cybercrime landscape.
- The site also sold access to proxies, which allowed criminals to further anonymize their web usage.
Importance Of Early Detection
In this post, we’ll cover how credit card fraud operates on the dark web, how criminals obtain and trade card data, and cover some essential prevention strategies. The forums also offer tutorials and guides on new hacking techniques as well as ways of improving existing skills. Therefore, such educational aspects attract a lot of aspiring cybercriminals who want to sharpen and take their abilities to the next level. Almost all dark web forum activities are illegal, and hence, the last thing users want is to reveal their real identities. Fortunately, the forums offer an option for users to operate under pseudonyms that help protect their identities. It’s the best way that users can make open communications as well as share sensitive data without exposing themselves.
- After all, cybercriminals can use the cards to buy items, extract the cash from the account, or just continue to charge the card itself until the bank realizes that the transactions are fraudulent.
- You can access deep and dark web data through our dark web API and perform detailed data analysis with Lunar.
- Its longevity and operational security practices contribute to its popularity and secrecy.
- These could be fraudulent sites made to mimic the real deal to steal your card details or login credentials.
- Dark-web marketplaces operate similarly to legitimate e-commerce sites, complete with customer reviews, vendor ratings, and escrow services, facilitating trust among criminals and enabling widespread illegal commerce.
CISOs Brace For Supply Chain Attacks With Proactive Attack Surface Monitoring
Carders may also create physical cards using the stolen details to carry out “card present” fraud, using them for in-store purchases. Whether online or offline, carders cover their tracks by using fake identities, donning disguises, or encrypting communications. For goods that need shipping, they often use drop addresses — places not tied to them — to dodge law enforcement. There’s also a high chance your stolen credit card info might end up on carding forums on the dark web, where bad actors sell and swap data and collaborate to level up their schemes. Dark web monitoring involves tracking activity on the dark web to identify potential threats such as stolen data, leaked credentials, and other sensitive information that could be harmful if accessed by malicious actors.
Some forums even provide escrow services to ensure secure transactions, where a trusted third party temporarily holds funds until both parties are satisfied with the transaction. However, the use of escrow services can vary across forums, and members often have to rely on their reputation and judgment to minimize the risk of being scammed. Carding forums are illegal dark web platforms where criminals can anonymously buy, sell, or trade stolen credit card information. Dark web marketplaces are central platforms for trading illegal goods and services, particularly related to financial fraud.
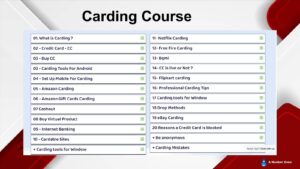
Hacking Tools
Ultimately, the strongest defense against credit card fraud involves ongoing vigilance, education, and collaboration among consumers, financial institutions, technology companies, and law enforcement agencies. By remaining proactive and informed, you can better protect your financial assets, identity, and peace of mind in an era of increasingly sophisticated cyber threats. As technology continues to evolve, so too will the methods criminals use to exploit credit card data, prompting an ongoing arms race between fraudsters and cybersecurity experts. The future landscape of carding will undoubtedly see significant shifts driven by emerging technologies, evolving criminal strategies, and proactive legislative efforts. Finally, criminals “cash out,” converting assets like resold electronics, gift cards, or cryptocurrencies into cash. This final stage completes the monetization cycle, allowing criminals to realize profits from stolen card information.
Carding can be over within minutes, with criminals — known as carders — taking off with stolen funds before you even notice. It usually starts with carders getting hold of your credit card details illegally and quickly verifying whether the card is active. If your card remains active afterward, your information could be sold on the dark web or repurposed for other financial crimes, like various forms of identity theft. A carding forum or carding website is an illegal site used to share stolen credit card data, and discuss techniques for obtaining credit card data, validating it and using it for criminal activity.
Risks And Challenges Associated With Buying And Selling Stolen Financial Data
Launched in September 2022, Torzon Market operates on the Tor network and features over 11,600 illegal products, including drugs and hacking tools. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet.
Another unique feature Brian’s Club has is the auctions it offers during which users can reserve, bid, and outbid other users who want to purchase exotic BINs. Active buyers are also eligible for free gifts and dumps depending on their volume. As one of the prominent platforms supporting such activities, card shops make carrying out such scams relatively easy and popular. The threat actor will need many more components, like binders or installers, to get their malware past defenses and onto the target networks. A threat actor might have the skills or motivation to complete all these parts of the process themselves, but it may be cheaper, quicker, and easier to hire a specialist to do it for them.
Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor. Unlike clear web forums, these communities not only facilitate communication, but they also facilitate the sharing and trading of various services and goods (most of which are usually illicit or illegal). Users need a specialized browser like Tor to access these forums, which provides anonymity and encryption to its users. Discover the top thirteen dark web forums where cybercriminals gather and cybersecurity researchers spot emerging threats. Malware can be used to steal credit card information by infecting devices to log keystrokes, intercept online transactions, or extract saved card details.



