
Though it is not illegal to visit the dark web, accessing it can expose you to serious legal risks, even if you don’t have any criminal activity in mind. However, with the right security measures and cautious browsing, you can minimize these dangers. If you engage in illegal activities or access illegal content that could implicate you in a criminal offense, you may face serious legal consequences, including fines and imprisonment. When you visit dark web sites, even if you don’t have any ill intentions, you support the dark web ecosystem, which serves as a medium to conduct various illegal activities.
But it’s recommended that you stick to Tor Browser still for true dark web access. It can access the regular internet through “outproxies,” but that’s not its strongest suit. I2P’s most attractive angle is to access its own internal eepsites, which are its version of .onion sites. It is definitely a strong contender for the best, strongest, layered encrypted web browser. This means you can use your favorite browser instead of the Tor Browser and still benefit from being routed through the Onion Network.
How Do Onion Routing And Tor Work?
Download the Linux version from torproject.org, extract the file, and run the start-tor-browser script. Secure communication for journalists, accessing privacy-focused forums, and whistleblower submissions. These secure communication platforms improve your security when using Tor. Practice safe, smart digital habits if you must use Tor to log into personal accounts. For instance, always use strong passwords that mix letters and symbols, making them hard to guess. Use different passwords for each account so that a single compromised account doesn’t affect others.
These features are accessible from the Freenet interface under the “Community” and “Tools” sections. And since most Dark Web sites are used for illegal purposes I am not going to offer any recommendations. It is at this point l leave you to your own devices and wish you good luck and safe surfing.
Understanding The Risks: Potential Dangers Of The Dark Web
Lewis points to the “first contact problem”, when an attacker spots when someone moves from non-private tools to private ones, noting it’s been used to identify whistleblowers. On the surface web, you can contact your credit card company or law enforcement for help. But the dark web operates like the Wild West—no rules, no protection. Threat actors also exploit vulnerabilities in your systems and software to gain access to them. So, you should also make sure that your system’s operating system and other installed software are patched with the latest updates. Suppose you share your name, social security number, or any other personally identifiable information on any dark website.

Keep Your Data Off The Dark Web
Also, its P2P routing design is more advanced and does not rely on a trustworthy directory to obtain route information. Furthermore, it has apps for almost every operating system, including Mac, Linux, Android, iOS, Windows, and Fire TV. The readers like you support Beencrypted to help keep up the good work. When you purchase using links on our website, we may earn an affiliate commission at no extra cost to you. The Tor Browser (also known as the Tor Browser Bundle) has been the de facto tool for connecting to the dark web for many years. It is the flagship product of the Tor Project (the company responsible for maintaining the Tor network).
Conclusion: Access The Dark Web Safely And Responsibly

Heck, I’m one of PCMag’s resident security experts, and I’m not playing around on the dark web just because I know how to. That’s why I’m not going to provide links or detailed instructions for accessing the internet’s shadier side. Many people use Tor to avoid surveillance by government agencies, ISPs, or other entities monitoring online activities. Similarly, people in countries with strict internet access and usage regulations must use Tor clients or virtual private networks (VPNs) to access some public websites.
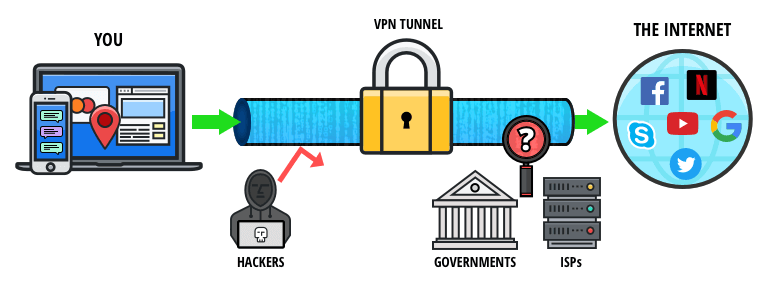
- For added protection, it’s best to use a VPN like ExpressVPN to encrypt your internet traffic and mask your IP address while establishing the initial Tor connection.
- As much as the dark web is supposed to promote free speech alongside bypassing censorship, many shady activities occur there.
- Freenet is still an experiment designed to resist denial-of-service attacks and censorship.
- It’s important to note that engaging in illegal activities is still illegal, even through the Tor network.
- If you use Tor to access the dark web or unblock websites, connect with a VPN for extra security.
Stand Up For Privacy And Freedom Online
You can’t open onion links via I2P, and you can’t open I2P links over a Tor network. Whether exploring the hidden internet for curiosity or privacy, these are the best dark browsers. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
Method II – VPN Over Tor
Moreover, it is best to cover your webcam with tape or paper if you are not using it. Sometimes, a dark web user on any of its open forums can also attempt a phishing attack to steal your personal information and further use it for financial gains or identity theft. Therefore, remaining vigilant and practicing caution on the dark web is crucial. A method of mitigating malware attacks is to ensure robust endpoint security. Make sure to protect your device with reliable anti-malware to mitigate such attacks.
Why Do The Darknet And Deep Web Exist In The World
Your ISP can see that you’re connected to Tor, as the encryption takes place AFTER you connect to the browser. With this information, the ISP will likely know you’re on the dark web because Tor is mainly used for this purpose. You don’t want this suspicion because of the darknet’s reputation and notoriety. You can enter .onion URLs directly into the Tor Browser’s address bar or visit directories like The Hidden Wiki to find popular sites on the dark web. Accessing the Tor network through Tails OS (The Amnesic Incognito Live System) on a thumb drive is a highly secure way to browse the dark web anonymously.
Is It Illegal To Use The Tor Browser?
For a number of technical reasons, it’s much faster and more reliable than Tor. The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method. In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous. The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely.
The websites are hidden in layers of encryptions and use dot (.) onion domains, which is why they are called onion sites. In this article, we have explored what the dark web is and how Tor Browser provides the necessary anonymity and encryption to access it. We discussed the importance of setting up Tor Browser correctly, ensuring security and anonymity, and navigating the dark web safely.
Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data. The dark web limits online tracking, and there are many legitimate reasons people like journalists and activists use the dark web to remain private. But there are also many illegal activities that happen on the dark web. And just like in real life, using the dark web for criminal purposes is never legal. The Hidden Wiki is a surface website offering a collection of dark web links.
- Instead of search engines, you’ll need to rely on directories or specific .onion links.
- However, while visiting the dark web itself isn’t against the law, engaging in illegal activities there is.
- If you need a way to organize as an activist or you want to discuss censored topics with others, my first suggestion is to stick to offline meetups.
- Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular.
- The Tor Browser is a specific web browser, based on Firefox, that utilizes the Tor protocol to enable private browsing.
Believe me – there are plenty to go around and each and every one of them are being kept under surveillance. Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers. Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows.



