The anonymity of the dark web makes it a fertile ground for coordinating cyberattacks and sharing illicit services without detection. The editorial team did not participate in the creation of this guide. Gizmodo may earn a commission when you buy through links on the site.
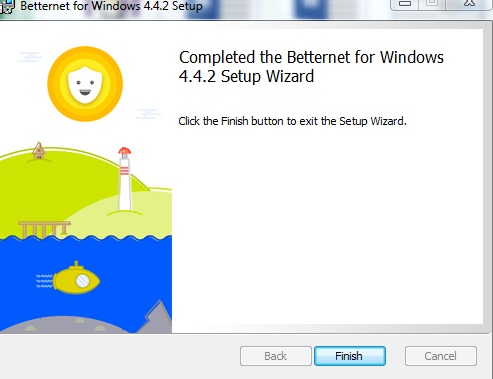
Use A VPN To Stay Safer On The Dark Web
Tor was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag. Tor was designed to protect American intelligence communications online. Tor Browser has since become a popular tool of journalists, activists, and others that may be subject to being monitored online. That’s a trick question, because there isn’t even a good free VPN, much less a best VPN.
Choose A Dark Web Search Engine
Since their deadline wasn’t met for the closer of the sites a month later, the Impact team ascended to the dark web, where they started to publish the data. The child pornography site Playpen is one of the famous scenarios that resulted from the dark web. The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users. If you live in the EU and want to know what data your provider has collected about you, the GDPR gives you the right to request a full report.
Understanding The Risks: Potential Dangers Of The Dark Web
- As mentioned, we recommend using a safe provider like NordVPN, which also offers Onion Over VPN servers perfect for accessing the dark web safely.
- If you must use one, ensure it’s a VPN with a strict, independently audited no-logs policy.
- ExpressVPN’s intuitive apps work on up to 8 devices at a time, ensuring protection for the entire family.
- This method is far more complex but we’ll still explain it for those too curious.
In 2025, each of these browsers presents unique strengths and limitations. Selecting the optimal tool depends primarily on your individual privacy requirements, technical expertise, and the specific contexts in which you plan to access the dark web. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails.
How To Use A VPN To Access The Dark Web
A VPN will give you an extra layer of protection and anonymity, making it much safer to explore the dark web. Unlike Tor, however, it cannot be used to access the public internet. It can only be used to access hidden services specific to the I2P network. I2P cannot be used to access .onion sites because it is a completely separate network from Tor.
It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check.
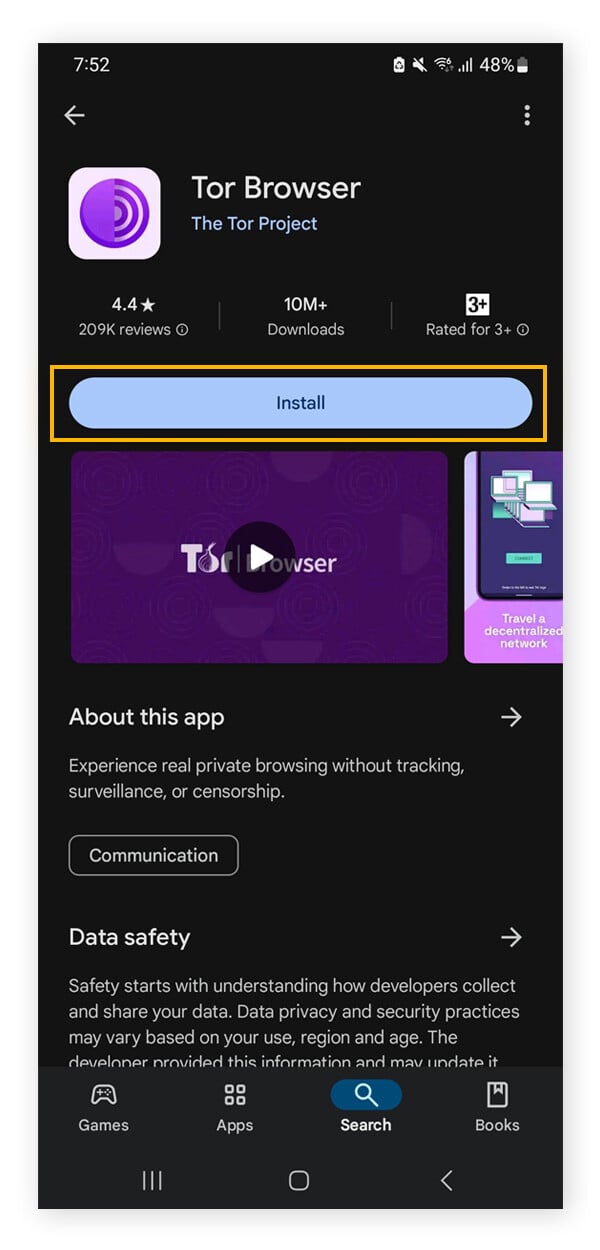
Another circumvention tool integrated into Tor Browser is “Snowflake,” which allows users to connect through temporary, ephemeral proxies, further aiding in bypassing network blocks. The choice of which circumvention method to use often depends on the specific nature of the blocking being encountered. Later, Tor’s underlying code was released under a free license, and a nonprofit called the Tor Project was formed. In 2008, the Tor Browser was released, which made it easy for anyone to get on the darknet.
Data Breach Websites
It is designed to provide online anonymity and privacy to its users. Journalists, activists, and individuals concerned about online privacy and security often use it. Accessing the Tor network through Tails OS (The Amnesic Incognito Live System) on a thumb drive is a highly secure way to browse the dark web anonymously. Tails is a portable operating system specifically designed for privacy, and it includes the Tor Browser by default. Here’s a step-by-step guide to setting up Tails on a USB thumb drive and using it to access Tor. In this setup, the VPN connection acts as a middle layer between your device and Tor, routing your internet traffic through the VPN before it reaches the Tor network.
One of the great things about Tor is that it can be used to access both the dark and surface web. Just note that although you’ll be anonymous, you won’t have the speed or convenience of a direct connection, and some sites might block you outright. When you open your default browser, Freenet will be ready and running through its web-based interface. Note you should use a separate browser than the one you normally use to help ensure anonymity. Obviously, finding these .onion websites is the first challenge, as they won’t show up in Google search results. You can’t just Google “Silk Road” and hope to land on the dark website.
The Best Dark Web Search Engines In 2024

The tradeoff is that you don’t get personalized search results, as DuckDuckGo doesn’t collect user data. But this tradeoff is worthwhile when seeking to browse with the utmost privacy. To surf the web privately, you need to connect to the Tor network from your browser.
Verified Social Channels And News Sites
It collects data from the public Tor network and archives historical data of the Tor ecosystem. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see.
Malware and scams are scattered like landmines around the dark web. And with many unfamiliar-looking sites on the dark web, it’s harder to distinguish safe websites from shady ones, and easier to fall victim. While some reports of dark web murder-to-order are overblown, it is possible to commission acts of cybercrime on the dark web. These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. Dark web domains tend to be inconsistent — new ones pop up and others disappear, which makes sense if they offer questionable or illegal goods and services. The dark web offers a fascinating glimpse into a hidden world, but navigating it requires vigilance.
What Are The Differences Between Tor Over VPN Vs VPN Over Tor?
Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. Other sites explicitly block search engines from identifying them. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing.
While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. Make sure that when you download the Tor file, it’s from their official website. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites.



