Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. Unlike regular online stores, these markets can shut down, change their URLs, or face law enforcement shutdowns frequently. Because of this it’s important to stay updated on which markets are active and which ones are no longer working.
You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. The first ever DNM — called Silk Road — was started in 2011 by U.S. citizen Ross Ulbricht.
Verified Market Links
Tor relays are servers run by volunteers, designed to keep your activities private and untraceable. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. The US Supreme Court has indicated that even casual browsing could lead to legal consequences. The Dark Web and Darknets offer valuable spaces if you value privacy, freedom of speech, or research security technologies.If you misuse them, the consequences can be severe.
Users’ identities are safe from the prying eyes of governments and corporations. The MITRE ATT&CK framework provides a comprehensive view of adversary tactics. Singularity™ Threat Intelligence provides insights into adversary tactics and helps mitigate these risks before they impact your organization.

Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Simply put, accessing and browsing the dark web is perfectly legal.
The History Of Darknet Marketplaces
Keep in mind that many criminal organizations use the dark web to communicate or sell merchandise. You may very well end up in the middle of a stakeout that could turn ugly. So, if the website looks fishy, close the tab, and forget about it. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use. Hidden Facebook is hardly the only social media client on the dark web. The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not.
You may also use it to access the regular internet more anonymously. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself.
Topics And Products Sold
The generalizability is specific to Hydra and may not apply to other darknet markets or regions. Russia’s unique socioeconomic context, for instance, influences drug trade dynamics differently than in other countries. Our proposed research approach can fix this by implementing it in other marketplaces in other countries. The region-specific data on the darknet drug trade, particularly in Russia, has been sparse. The traditional and new ways of distribution social networks and messengers like Telegram and WhatsApp are not covered in this study.
Subscribe To The Blog Newsletter
These sites attract thousands of users every day, offering all kinds of illegal goods that keep the underground trade going. Most buyers and sellers use the Tor network, which hides IP addresses and locations. Doing so makes it harder for authorities to identify who’s behind a purchase or a listing. Vendors often build up reputations through ratings and reviews, just like sellers on mainstream platforms. To reduce scams, many markets also use escrow systems, where the site holds the buyer’s payment until they confirm the item has been delivered. Bazaar marketplace is known for a wide range of products (drugs, fraud tools) and a straightforward interface.
The Types And Combinations Of Drugs Discovered In This Paper
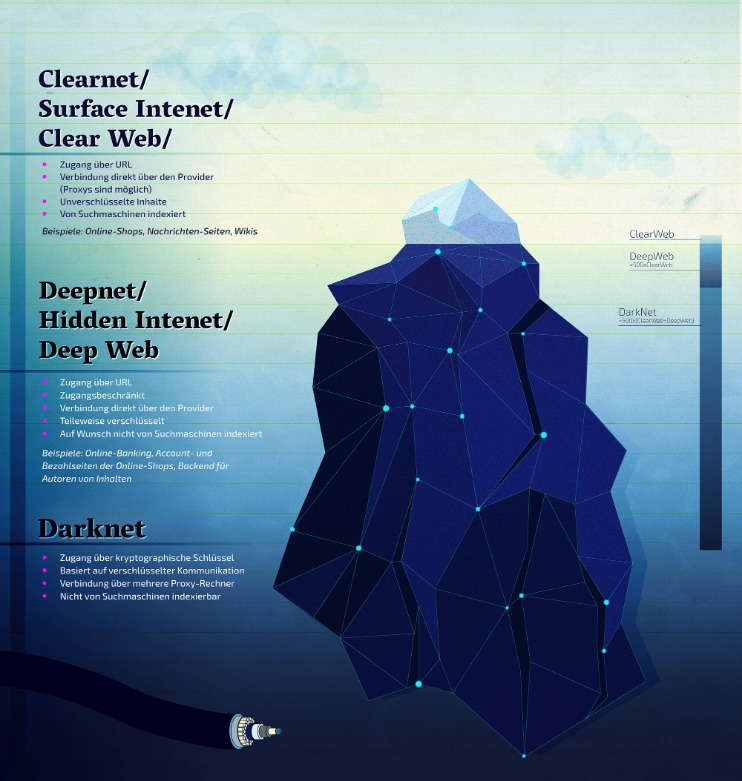
For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. So, if you want to know how to access the dark web safely, you need to understand that the vast majority of the dark web, or dark net, is only accessible through the Tor browser. It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content.

Newsletters
You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked. These tools scan dark web forums and marketplaces for any signs of your compromised credentials. There is no need to visit darknet marketplaces yourself to know whether your data was leaked.

- Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums.
- The most interesting thing about NordVPN is its built-in Onion over VPN feature.
- Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace.
- As stated above, we don’t condone any activity—on the dark net or otherwise—that is forbidden by law.
- Consider Abacus darknet as a study case to research secure marketplaces.
It also requires users to verify their identity carefully to build trust with buyers focused on fraud. You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions. If you plan to purchase on a dark net marketplace or dark web commerce sites, you’ll need to create a fake identity.
- Hence, it should be the top priority to track these platforms and shut them down as quickly as possible.
- And because there’s very little use of HTTPS on the dark net, verifying whether or not a website is genuine using an SSL certificate is not feasible.
- Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either.
- The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers.
- Articles from JMIR Formative Research are provided here courtesy of JMIR Publications Inc.
- It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself.
Some services are genuine; you can get what you want at an agreed fee. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Therefore, the legality of the dark web will mainly depend on how you use it.
Anonymity Through Tor
Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. These domain names are not registered with a central authority but are instead derived from cryptographic keys. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. Following the NYT, the BBC launched a dark web “mirror” of their international edition in 2019.



