
In this post, we’re going to narrow down the differences between all of them and will try to picture how they are different from each other. The Dark Web and Darknets offer valuable spaces if you value privacy, freedom of speech, or research security technologies.If you misuse them, the consequences can be severe. Even platforms like Netflix, which require paid access, are technically part of the Deep Web.
Examples Of Dark Web Resources
For example, journalists who researched the dark web were shocked to find that it already had lots of info on them. To access the dark web, you’ll need special search engines like Candle, Not Evil, and SearX, all of which require a specialized browser like Tor to work. On the dark web, neither users nor web administrators reveal themselves to each other, including their identity or their location. Hence, it’s very hard to shut down dark web servers or place geo-restrictions on users. On the Deep Web, these risks primarily relate to the fact that you need to authenticate to access a private site and that these sites contain a great deal of sensitive and valuable personal data.
- As for the dark web, it’s intentionally hidden, encrypted, and made anonymous.
- The Dark Web is also where cybercriminal gangs commonly congregate and plan their attacks.
- While the technology that underpins it has valid applications for privacy and anonymity, it also draws criminal elements who exploit that same anonymity.
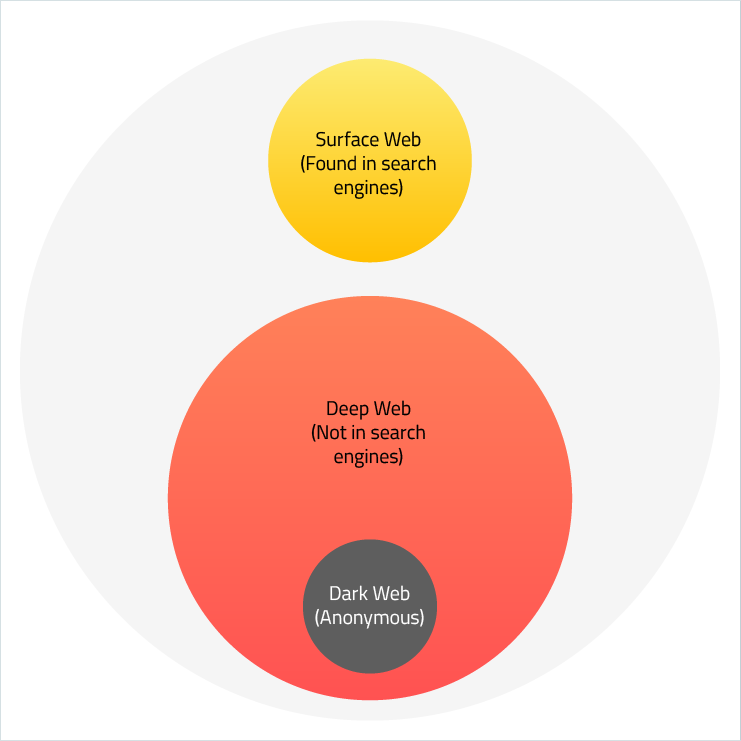
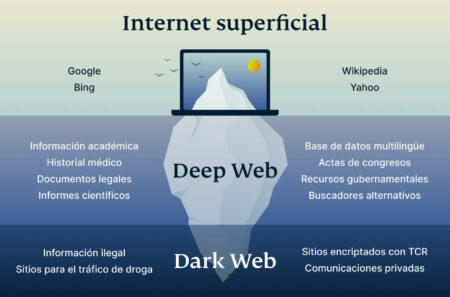
- The deep web is all the webpages on the internet that aren’t publicly available or accessible.
Any website that does not have a link to it can be considered to be a part of the deep web and it accounts for 90 percent of the web. A lot of people use the terms “dark web” and “deep web” in tandem with illegal and unsafe activities on the internet. However, the reality is these places are very different and have a warped public perception. While they do host criminal activities, chances are you won’t stumble onto anything unless you go in very far. Organizations of all sizes, even large enterprises, can regularly leak sensitive data via public GitHub repos.
What Is Threat Hunting?
For this reason, all the access data must be indexed through any search engine. Now let’s understand the basics of the Indexed web for better clarity. There’s also a risk of being monitored by state actors or cybercriminals who leverage de-anonymization techniques to identify users. This exposure can lead to legal repercussions if law enforcement tracks illegal activities back to you, despite the anonymity. Understanding the difference can help you avoid potential risks and stay secure online.
How Do You Access The Dark Web?
This also makes it a valuable source of information regarding emerging cybersecurity risks and data breaches. The most popular dark web network is The Onion Network (TOR network). There are several others, but none with as large a user base as TOR. Accessing the TOR network requires a special web browser called a TOR browser. The TOR network allows people to access private, specially encrypted pages ending in ”.onion”.
Cybercriminals, internet scammers, hackers, and internet brokers use it for lethal purposes. People use the Dark web for purposes of Human trafficking, hiring hitmen, selling weapons and drugs, child pornography, racist content, and content that speaks hate about minorities and otherwise. One cannot reach the Dark Web so easily since they have created strong encryption that is unreachable to the average user. The risks of accessing the deep web vs. the dark web may be similar but not exactly the same.
What’s The Difference Between Deep Web & Dark Web?

Scammers often target users on the dark web, employing phishing tactics to steal personal information and financial details. These scams can result in significant financial loss and identity theft. The danger comes in when you download illegal materials that contain viruses or malware, like trojans, worms, or keyloggers. When navigating beyond the surface web, there are a few key differences to keep in mind when venturing into the deep and dark web. The deep web provides users a level of security or privacy, but it can’t offer full anonymity. In order to have that, you’ll need to go one step further down into what is called the dark web.
Subscribe To Our Newsletter!
- It’s possible that, as people become more aware of the different entities they describe, confusion will die down.
- Beneath the familiar websites lie layers of content that most users know little about.
- But the dark web isn’t a violent or criminal place in and of itself — it just depends on how you use it.
- As mentioned earlier, regular browsers cannot access dark web websites.
- The information that one shares through Tor are always encapsulated through secure tunnels like onion layers to reach its destination.
Therefore, before we get started with the comprehensive details of Dark and Deep websites, you first need to educate yourself about the Surface Web better. Once in a lifetime, you would come across these complicated terms like Deep Web and Dark Web on the internet and throw yourself in confusion. However, to keep you from getting appalled, I have designed this blog to teach you in-depth knowledge of the Deep Web vs Dark Web and its mysterious functionality.
What Are Some Examples Of Deep Web Websites?
Without visibility and dark web intelligence, security teams can only wait and hope their network defenses are sufficiently robust. This situation challenges risk analysts and security teams to discover leaked credentials and gather threat intelligence. Companies need to update their threat prevention techniques to monitor dark web environments. However, using the deep web for legitimate reasons is uncontroversial. Start a free 30-day trial of Keeper Password Manager today to begin securing your accounts from common cyber threats on all parts of the internet. One dark web monitoring tool that works alongside Keeper Password Manager is BreachWatch®.
August’s Top VPN Discounts
Phishing is when someone contacts you pretending to be someone else to gain access to your personal information, which often results in identity theft. Deep and Dark Web are two different concepts, but easy to understand. The Dark Web is not illegal to use or consists entirely of illegal elements. The news that will amaze you is that the internet you use contains only 10% of the global internet, and the Dark Web occupies 90% of the space.
What Is A Managed Cybersecurity Service?
When you access the dark web, everything stays internal on the Tor network, which provides security and privacy for everyone equally. This is both good and bad, and is why criminal activty is so widespread on it. Many worldwide concerns have arisen from it, one of the most notable being the infamous Silk Road—which is a marketplace for obtaining all sorts of goods. The surface web is also called visible web, or Indexed Web is the web that we use on a day-to-day basis. It is where our daily online activities take place, and what most people consider as the Internet. The dark web is the traditional place for threat actors to engage in cybercrime through selling stolen credentials, sharing guides for techniques, posting ransomware victims’ information, and more.
Misconception 2: “All Dark Web Activity Is Illegal”
Darknet provides a user with anonymity but service was introduced that allowed someone to host a website on the darknet and remain anonymous. This attracted people who do illegal stuff to sell things without getting caught. One example is a website called the silk road which was on a darknet called TOR, used to sell drugs, and was taken down by the FBI. On the other hand, accessing the dark web requires special software, most commonly Tor, which masks your identity and provides access to websites with .onion extensions. Surface web search engines do not index these sites, so you need the right tools to navigate safely and anonymously. The dark web is home to all sorts of illicit activities and is considered unsafe.
Firstly, we should clarify what is legally permitted when investigating dark web threats. Companies can passively monitor activity and data sales on dark web marketplaces. They detect stolen employee logins, customer data, postal addresses, social security numbers, and other valuable personal data relating to your business operations. Data protection increasingly requires active dark web monitoring to manage compliance risks.
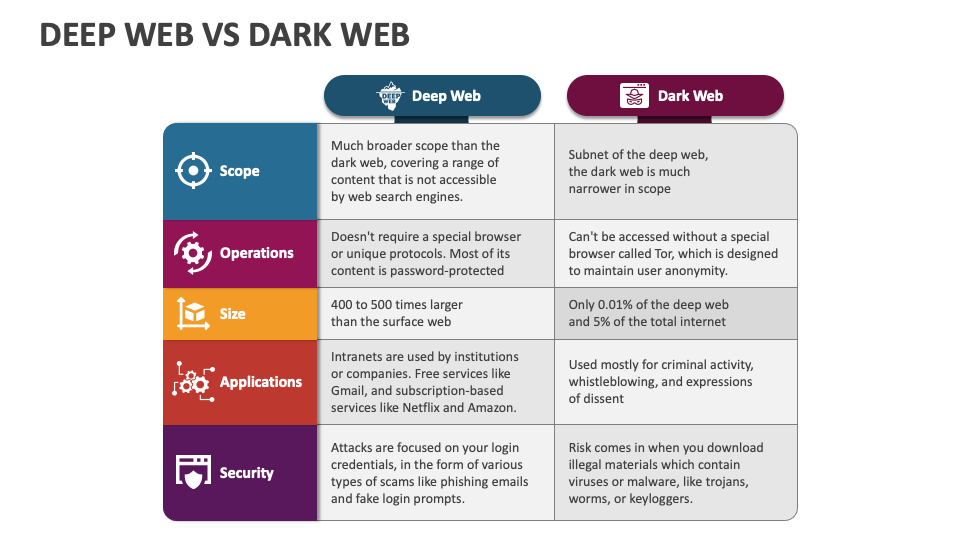
While this makes it a popular choice for privacy-focused users, it also opens the door to hidden risks. Although Tor and similar tools offer another layer of protection, the dark web’s lack of regulation and hotbed of illegal activity can expose users to scams, malware, and other hidden threats. The deep web refers to any part of the internet that is not indexed by traditional search engines like Google or Bing. This includes content that is behind paywalls, logins, or dynamic queries—essentially anything you can’t access without credentials or a direct URL.
When a user and a website send data to each other over Tor, the data packets are randomly routed through a massive network of volunteer computers. Each of these nodes only knows where the packet just came from and where it’s going next, as each layer of an encryption onion is stripped from the packet contents. It’s only when the packet reaches the final destination that the last layer of encryption is removed and the intended recipient gets the original data. The dark web is also legal to access, but it comes with serious risks. While there are legitimate uses, much of the content hosted there involves illegal activity, including drug trafficking, illicit imagery, and the sale of stolen data. Browsing without caution can expose you to this content, and even unintentionally engaging with it may result in legal consequences.



