First, you need a web browser that’s capable of utilizing the Tor protocol. That means that if your incoming traffic is routed through a node operated by cybercriminals, they can inject malware into the code of the response, without you ever knowing that it’s happened. The reason why the deep net provides this level of privacy for website hosts is that the .onion address that you use to access the website obfuscates the actual IP address of the server. This makes it impossible to track down the physical server under ordinary circumstances.
Tips To Stay Safe When Using The Dark Web
You could be monitored closely even if you are not doing anything illegal. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography.
Deep Web: Definition, Benefits, Safety, And Criticism
You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software. This article lists some of the best dark web websites you can visit securely. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun.
Privacy Protection:
Hacker services against banks and other financial institutions are offered there. Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito.
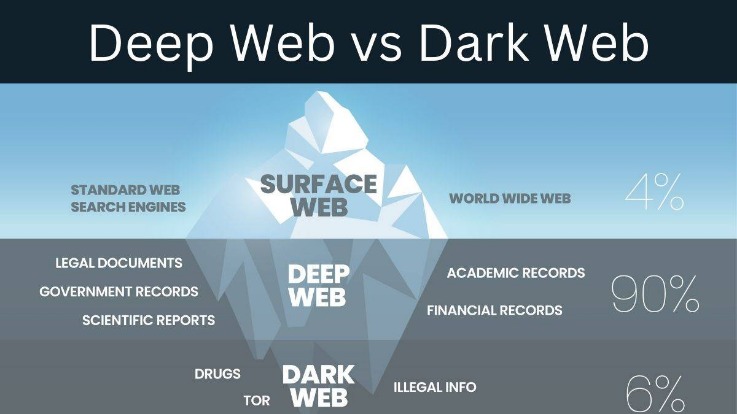
What Is The Deep Web Vs Surface Web: Comparison
Further, monitoring exchanges on dark web forums allows security personnel to gather threat intelligence. This enables them to gain insights into the operations of sophisticated adversaries and be warned of emerging threats. However, Tor does not establish a direct connection between the user endpoint and the internet.
By following the tips for safe exploration and being aware of the common misconceptions, individuals can navigate the Deep Web responsibly and make the most of its hidden treasures. Just as in the surface web, the Deep Web is not immune to malware and other cybersecurity threats. To protect yourself, ensure that your antivirus and antimalware software is up to date. Regularly scan your device for potential threats to maintain a secure online experience. While Tor provides significant privacy benefits, it is essential to use the network responsibly.
A Dark Web Search Engine
Put simply, the Dark Web is any site, messaging platform, community, or other online entity that is not indexed by any search engine. A subset of the Deep Web, the Dark Web is intentionally hidden from your standard search engines, and is much more difficult to access as all its data is encrypted. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc.
Data Link Layer
The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. Most likely, the native account on your device has full admin permissions by default.
This anonymity is not necessarily used exclusively for illegal activity. For instance, political dissidents under an oppressive government might use the dark web for communication. It is tremendously more vast than the surface web, with some experts estimating that search engines index less than 1% of online content. Unlike the dark web, which is deliberately obscured by layers of technology, the deep web exists just below the surface web. The majority of the deep web consists of regular websites that require users to create an account before they can be accessed. The dark web is a subsection of the deep web including websites that one can only access through purpose-built web browsers.
- Cybercriminals, law enforcement, etc., all of these and more might closely observe who chooses to enter that dubious digital realm.
- The Deep Web consists of all information on the World Wide Web which cannot be located by general-purpose search engines (Google, Yahoo, Bing etc.).
- Universities, research institutions, and libraries house vast digital archives of theses, dissertations, journal articles, and raw data—most of which are not indexed by search engines.
- All the scams you can fall prey to on the surface web apply to the dark web.
It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. However, this feature is only available on iOS, Android, and Windows. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there.
Whenever you’re on a dark web site, avoid dropping any personal information. Create anonymous profiles for any website you register with on the dark web. Additionally, ensure you do not visit websites or social media that might require you to drop your personal details. To discover content on the web, search engines use web crawlers that follow hyperlinks through known protocol virtual port numbers.
Most Dark Web users use the TOR browser, which is designed to make the Dark Web easier to navigate. The TOR browser provides improved privacy and anonymity on the public Internet and makes it possible to access .onion sites on the Dark Web. The Dark Web is designed to provide privacy and anonymity to its users by encrypting and anonymizing the traffic by using darknets. However, these features can be used for both legitimate and malicious purposes. This is the primary reason why the US NRL developed the TOR technology used by most Dark Web visitors.
- For instance, political dissidents under an oppressive government might use the dark web for communication.
- Conventionally, Nord also doesn’t log your data and uses AES 256 encryption.
- The fact that this data resides in the Deep Web does not necessarily guarantee its ethical use.
- While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity.
Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device. Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web.

On the contrary, these sites makes use of .onion extensions, which can only be accessed on an onion-supported browser such as Tor. Note that the dark web sites do not have extensions such as .com / .net / .org etc, as these are clearnet domain extensions and can be traced quite easily. Despite the advanced features and capabilities of the Tor network, accessing the same is quite easy, all you need is the Tor Browser. The “Dark Web” is what people are “actually” referring to when they’re talking about the dangerous, illegal deep web.
Using our ocean and iceberg visual, the dark web would be the bottom tip of the submerged iceberg. At the dark end of the web, you’ll find the more hazardous content and activity. Tor websites are located at this far end of the deep web, which are deemed the “dark web” and are only accessible by an anonymous browser. The most infamous of these onion sites was the now-defunct Silk Road, an online marketplace where users could buy drugs, guns and all sorts of other illegal items. The FBI eventually captured Ross Ulbricht, who operated Silk Road, but copycat sites like Black Market Reloaded are still readily available. Tor is software that installs into your browser and sets up the specific connections you need to access dark Web sites.



