
Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top. To get on the dark web, you need a browser built for the job, and the best in the business is Tor.
The 9 Most Private Cryptocurrencies In 2025

Such data includes medical records, financial information, research papers, private forums and networks, and other content. The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted. Using a VPN (Virtual Private Network) in tandem with the Tor browser ensures an added layer of security by encrypting your traffic before it reaches the Tor network. Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. A virtual private network (VPN) is a good way to mask Tor activities.
Use A Dedicated Browsing Machine
- The dark web addresses are a randomly-scrambled sequence that generates URLs, mostly hard to remember ones.
- The Tor Browser also features many built-in protections that protect against tracking and fingerprinting.
- Onion sites may offer secure access to cryptocurrency wallets or anonymous email clients.
- When the message reaches the final node, it once again appears complete.
- Websites within the dark web often utilize unique addresses ending in .onion, which are exclusive to the Tor network and cannot be accessed via standard web browsers.
- Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web.
For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption.
Server-side Restrictions

It also has 10 simultaneous connections, support for all devices, and server obfuscation that works in China. You’ll appreciate its added features, such as Threat Protection, which shields you from malware and trackers. NordVPN also includes Double VPN servers to double your encryption and make you untraceable. One of its key benefits is unlimited bandwidth, which sounds awesome and allows for unlimited dark web browsing.

Step 4: Adjust Security Settings
People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user.
Power BI Classes In Pune Learn Data Visualization From Experts – Bes
That’s why knowing which dark web websites are safe to visit is vital. Each node in the Tor circuit only knows the IP address of the node directly before and after it, never the entire path. This segmented design makes it extremely difficult for any observer, whether it’s a website, ISP, or malicious actor, to trace your traffic back to you. While Tor offers strong privacy protections, it comes with notable drawbacks that can make it impractical for everyday use, and the dark web content it grants access to can put users at risk. By using a VPN to connect to Tor — a special browser designed to access the dark web — you can securely access the dark web using a technique known as Tor-over-VPN.
- Formerly, Darren served on the Committee of Technology Infrastructure under Mayor Richard Daley.
- Understanding the strengths and limitations of each solution helps you select the best tool for your specific needs.
- Furthermore, it is strongly recommended to avoid downloading any files from the dark web unless absolutely certain of their safety and origin.
- This has led authorities to confiscate computers of volunteers who simply host Tor nodes; some of the nodes have also been shut down.
- The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data.
What Is Tor And Why Is It Called “The Onion Router”?
The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search. So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.
Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web.

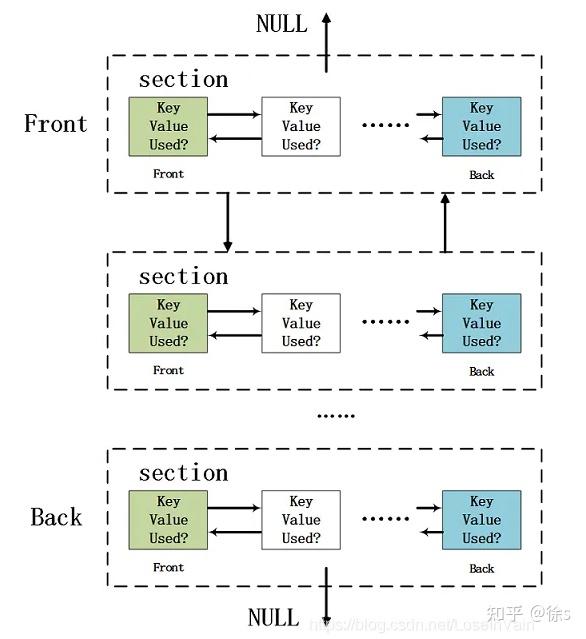
Since each node server in the Tor network is volunteer-operated, you never know who operates the relays that your data is traveling through. While this isn’t an issue for most of the trip (since each relay only has access to the previous and next relays in the network), it is an issue with the exit node. Because of the relaying of data through the onion nodes, and the encrypting and decrypting taking place at each node, your internet connection will slow considerably.
Is Accessing The Dark Web Illegal In India?
For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity.
They know how to process the information and get it to the correct law enforcement agencies internationally. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user.
The dark web offers a fascinating glimpse into a hidden world, but navigating it requires vigilance. For beginners, this guide sets the foundation, and for further exploration, check out our Top Darknet Markets to dive deeper into this ecosystem. We’ve compiled a detailed guide to help you explore the Top Darknet Markets. Discover the most trusted platforms like Anubis Market, and more, complete with their unique features and security measures.



