
He has worked for several international tech platforms, and his writing and editing expertise has also enhanced over time. He loves covering topics about VPNs, online privacy, and anonymity and shares his knowledge of online security with internet users through his words. With NordVPN’s double VPN feature, your traffic is routed through two servers for double encryption. It also includes a dark web monitoring feature that crawls the dark web and alerts you if your details show up anywhere. For these reasons, it’s a good idea to safeguard your online activities with NordVPN while using the dark web.
The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. I2P can only be used to access hidden sites that are only available on the I2P network. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor.
Although oceans cover more than 70% of our planet, we have only explored 5% of it. That’s only a fraction of what’s out there, which is identical to what’s available to the general public on the surface web. For example, you can only find your Facebook friends, photos, and other information by logging into your Facebook account and finding the information there. On the deep web, you can find such “private” information on web pages.
Keep Your Data Off The Dark Web
Beneath the familiar websites lie layers of content that most users know little about. Among these layers, the terms “Deep Web” and “Dark Web” often surface in discussions about internet safety and privacy. To access the purposely hidden part of the internet, you have to use special tools such as the Tor browser.
Hacking Groups And Services
When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI. The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor.
Therefore, you should stay cautious and avoid clicking when accessing the dark web. Doing so will protect you from accidentally accessing illicit content or becoming a victim of malware. Additionally, much of the materials on the dark web are illegal, and unknowingly downloading such content can implicate you in criminal activities punishable by laws. If your device is infected with malware, read our guide to remove malware from your computer.
Are Sites On The Dark Web Illegal To Use And Visit?
Dark web websites don’t bear Internet Corporation for Assigned Names and Numbers (ICANN) domains, such as .com. They use a scramble naming structure that combines a string of letters and numbers to create URLs that are impossible to remember. If your incoming traffic passes through a node run by cybercriminals, they could inject malware into the response code. If your device is unprotected, you could be a victim of malware or a hacking attack. You can never be sure of the motive of the person operating the node that your traffic is routed through.

In theory this should make your deep web browsing (as well as your regular web browsing) entirely private from interlopers. However, since your traffic is routed through nodes that you don’t have any control over, you are at the mercy of whoever operates these nodes. The terms “deep web” and “dark web” are commonly used interchangeably.
Commercial Services
To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. If found, take immediate steps to secure your accounts and personal information. As always, protect yourself from online threats with mobile Android security or iOS security software. And use a VPN for Android or a VPN for iOSto get a secure, private connection. The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people).
Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. Tor is like the public-facing door to the dark web, and there are even mobile apps for Android and iOS. Despite its depths, not all of the deep web poses a threat; indeed, much of it enhances global knowledge and educates individuals participating in specialized fields. Due to the anonymity of the seller and buyer, these marketplaces are full of fraudulent sellers.
Are There Any Other Names For The Surface Web?
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk. This is because law enforcement often actively monitors these sites. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing.
- It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers.
- Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material.
- But the so-called “visible” Internet (aka surface web or open web) — sites that can be found using search engines like Google and Yahoo — is just the tip of the iceberg.
- It comprises websites, resources and services that aren’t indexed by regular web crawlers.
Onion Links: How To Access Them
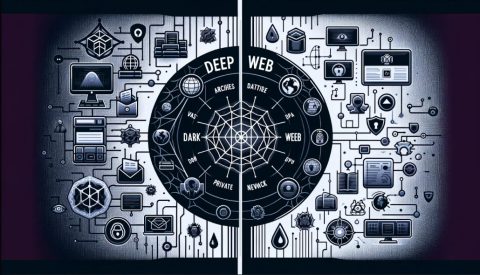
The part that we are most familiar with is really just what we might think of as the surface web. This includes sites we regularly visit, be it our social media networks, news outlets, or e-commerce sites – indexed by traditional search engines like Google or Bing. This very well-known territory hides a lot more – a giant called the deep web and an even smaller part called the dark web. The dark web is a hidden part of the internet not indexed by regular search engines, accessed through specialized browsers like Tor. It hosts both legal and illegal activities, offering anonymity but also posing risks like scams and illicit content. The dark web is a small part of the much larger “deep web,” which also isn’t indexed by search engines — but authorized users can access it using common web browsers.

- The platform is protected from government interference and malicious attacks to protect the user.
- The privacy offered by the Tor browser is important in the current digital age.
- Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble.
- The advantage of this version is that you can effectively create a Facebook account anonymously or use this social media platform in a restricted region.
- Formerly known as Archive.is, it is one of the best onion sites on the dark web.
The vast majority of the internet exists outside the realm of a Google search, and the first layer below the surface-level internet is what is called the deep web. If you need a great Tor VPN, I recommend ExpressVPN — all its servers allow Tor traffic, it has excellent security and privacy features, and it provides fast browsing speeds. SecureDrop is an open-source submission system that nonprofit organizations (NGOs), journalists, and news organizations can use to share and receive sensitive files securely. It’s used by 50+ news organizations, including ABC, Bloomberg News, CBC, and The New York Times. Darknetlive contains articles about everything related to the dark web.
The 5 Best Free Password Managers Of 2025
It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Tor is by far the most widely used dark web network and is the biggest network in terms of content and activities. The dark web often connotes illicit activities like illegal drug sales and hacking. However, it also supports legitimate uses like protecting free speech and accessing information in censored regions. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news.
Disgruntled Developer Gets Four-year Sentence For Revenge Attack On Employer’s Network
If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites. Unlike other search engines, it does not collect or share web activities and personal data of users. The Deep Web includes unindexed content like private databases and password-protected sites accessible with standard browsers.



